The cybercriminals in control of Kimwolf — a disruptive botnet that has infected more than 2 million devices — recently shared a screenshot indicating they’d compromised the control panel for Badbox 2.0, a vast China-based botnet powered by malicious software that comes pre-installed on many Android TV streaming boxes. Both the FBI and Google say they are hunting for the people behind Badbox 2.0, and thanks to bragging by the Kimwolf botmasters we may now have a much clearer idea about that.
Our first story of 2026, The Kimwolf Botnet is Stalking Your Local Network, detailed the unique and highly invasive methods Kimwolf uses to spread. The story warned that the vast majority of Kimwolf infected systems were unofficial Android TV boxes that are typically marketed as a way to watch unlimited (pirated) movie and TV streaming services for a one-time fee.
Our January 8 story, Who Benefitted from the Aisuru and Kimwolf Botnets?, cited multiple sources saying the current administrators of Kimwolf went by the nicknames “Dort” and “Snow.” Earlier this month, a close former associate of Dort and Snow shared what they said was a screenshot the Kimwolf botmasters had taken while logged in to the Badbox 2.0 botnet control panel.
That screenshot, a portion of which is shown below, shows seven authorized users of the control panel, including one that doesn’t quite match the others: According to my source, the account “ABCD” (the one that is logged in and listed in the top right of the screenshot) belongs to Dort, who somehow figured out how to add their email address as a valid user of the Badbox 2.0 botnet.
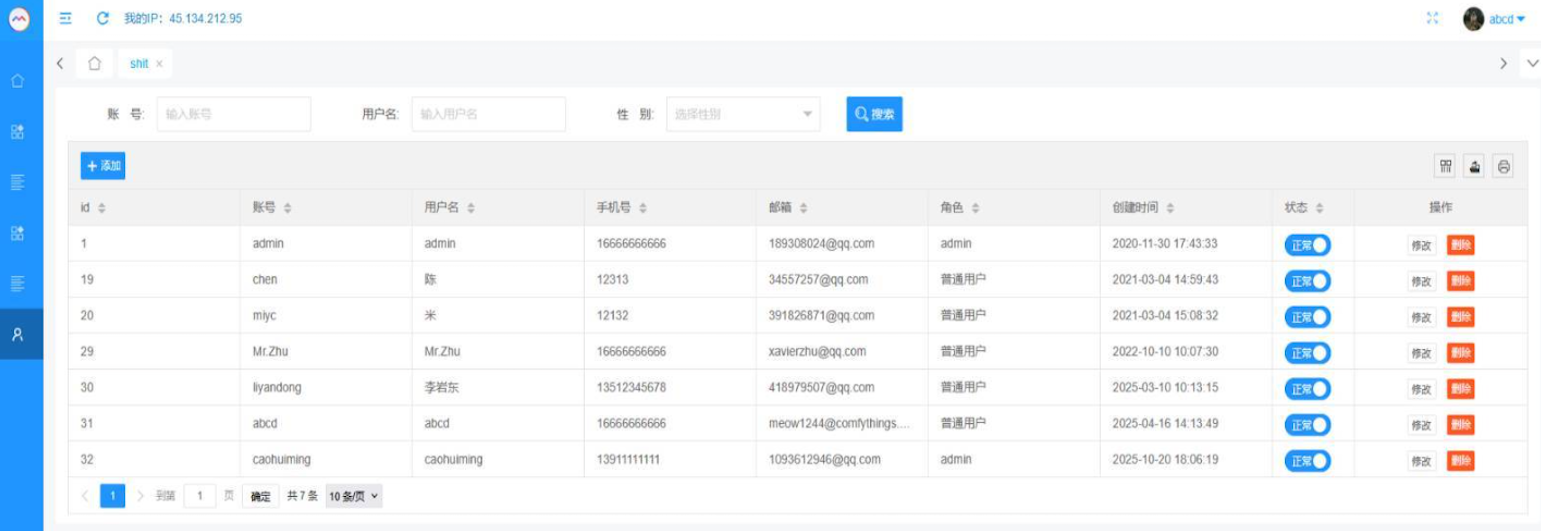
The control panel for the Badbox 2.0 botnet lists seven authorized users and their email addresses. Click to enlarge.
Badbox has a storied history that well predates Kimwolf’s rise in October 2025. In July 2025, Google filed a “John Doe” lawsuit (PDF) against 25 unidentified defendants accused of operating Badbox 2.0, which Google described as a botnet of over ten million unsanctioned Android streaming devices engaged in advertising fraud. Google said Badbox 2.0, in addition to compromising multiple types of devices prior to purchase, also can infect devices by requiring the download of malicious apps from unofficial marketplaces.
Google’s lawsuit came on the heels of a June 2025 advisory from the Federal Bureau of Investigation (FBI), which warned that cyber criminals were gaining unauthorized access to home networks by either configuring the products with malware prior to the user’s purchase, or infecting the device as it downloads required applications that contain backdoors — usually during the set-up process.
The FBI said Badbox 2.0 was discovered after the original Badbox campaign was disrupted in 2024. The original Badbox was identified in 2023, and primarily consisted of Android operating system devices (TV boxes) that were compromised with backdoor malware prior to purchase.
KrebsOnSecurity was initially skeptical of the claim that the Kimwolf botmasters had hacked the Badbox 2.0 botnet. That is, until we began digging into the history of the qq.com email addresses in the screenshot above.
An online search for the address 34557257@qq.com (pictured in the screenshot above as the user “Chen“) shows it is listed as a point of contact for a number of China-based technology companies, including:
–Beijing Hong Dake Wang Science & Technology Co Ltd.
–Beijing Hengchuang Vision Mobile Media Technology Co. Ltd.
–Moxin Beijing Science and Technology Co. Ltd.
The website for Beijing Hong Dake Wang Science is asmeisvip[.]net, a domain that was flagged in a March 2025 report by HUMAN Security as one of several dozen sites tied to the distribution and management of the Badbox 2.0 botnet. Ditto for moyix[.]com, a domain associated with Beijing Hengchuang Vision Mobile.
A search at the breach tracking service Constella Intelligence finds 34557257@qq.com at one point used the password “cdh76111.” Pivoting on that password in Constella shows it is known to have been used by just two other email accounts: daihaic@gmail.com and cathead@gmail.com.
Constella found cathead@gmail.com registered an account at jd.com (China’s largest online retailer) in 2021 under the name “陈代海,” which translates to “Chen Daihai.” According to DomainTools.com, the name Chen Daihai is present in the original registration records (2008) for moyix[.]com, along with the email address cathead@astrolink[.]cn.
Incidentally, astrolink[.]cn also is among the Badbox 2.0 domains identified in HUMAN Security’s 2025 report. DomainTools finds cathead@astrolink[.]cn was used to register more than a dozen domains, including vmud[.]net, yet another Badbox 2.0 domain tagged by HUMAN Security.
A cached copy of astrolink[.]cn preserved at archive.org shows the website belongs to a mobile app development company whose full name is Beijing Astrolink Wireless Digital Technology Co. Ltd. The archived website reveals a “Contact Us” page that lists a Chen Daihai as part of the company’s technology department. The other person featured on that contact page is Zhu Zhiyu, and their email address is listed as xavier@astrolink[.]cn.
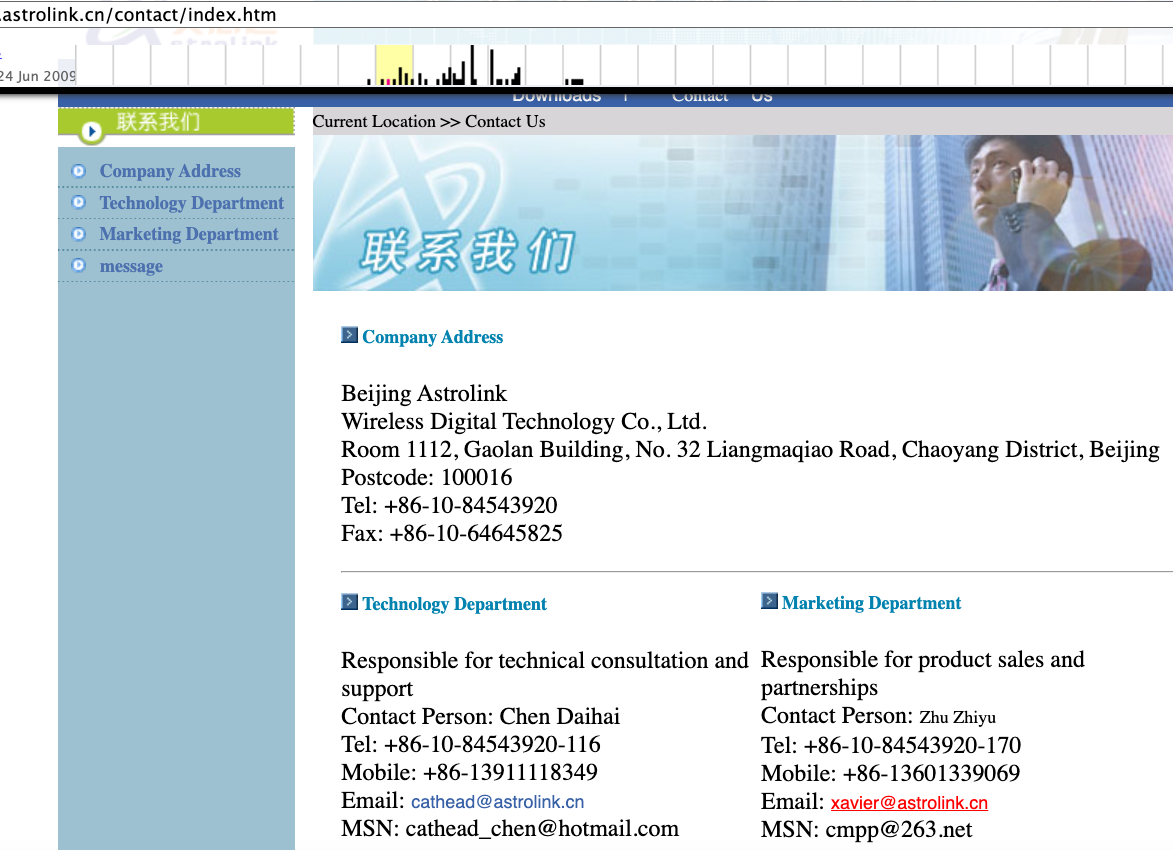
A Google-translated version of Astrolink’s website, circa 2009. Image: archive.org.
Astute readers will notice that the user Mr.Zhu in the Badbox 2.0 panel used the email address xavierzhu@qq.com. Searching this address in Constella reveals a jd.com account registered in the name of Zhu Zhiyu. A rather unique password used by this account matches the password used by the address xavierzhu@gmail.com, which DomainTools finds was the original registrant of astrolink[.]cn.
The very first account listed in the Badbox 2.0 panel — “admin,” registered in November 2020 — used the email address 189308024@qq.com. DomainTools shows this email is found in the 2022 registration records for the domain guilincloud[.]cn, which includes the registrant name “Huang Guilin.”
Constella finds 189308024@qq.com is associated with the China phone number 18681627767. The open-source intelligence platform osint.industries reveals this phone number is connected to a Microsoft profile created in 2014 under the name Guilin Huang (桂林 黄). The cyber intelligence platform Spycloud says that phone number was used in 2017 to create an account at the Chinese social media platform Weibo under the username “h_guilin.”
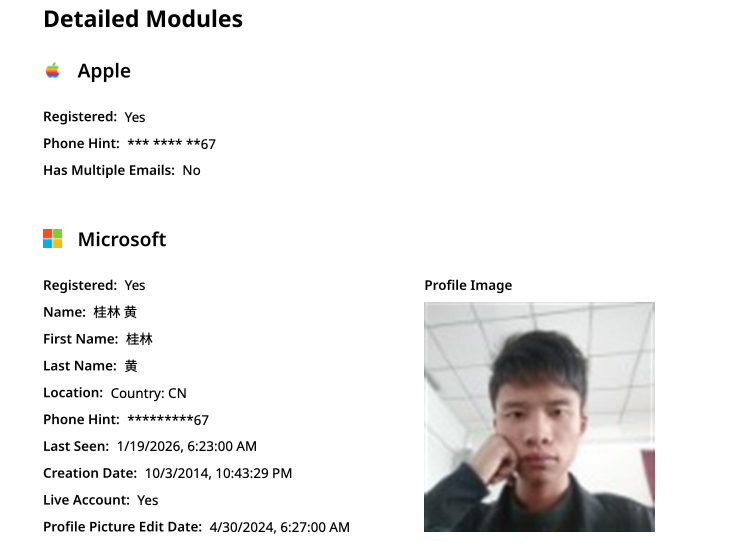
The public information attached to Guilin Huang’s Microsoft account, according to the breach tracking service osintindustries.com.
The remaining three users and corresponding qq.com email addresses were all connected to individuals in China. However, none of them (nor Mr. Huang) had any apparent connection to the entities created and operated by Chen Daihai and Zhu Zhiyu — or to any corporate entities for that matter. Also, none of these individuals responded to requests for comment.
The mind map below includes search pivots on the email addresses, company names and phone numbers that suggest a connection between Chen Daihai, Zhu Zhiyu, and Badbox 2.0.
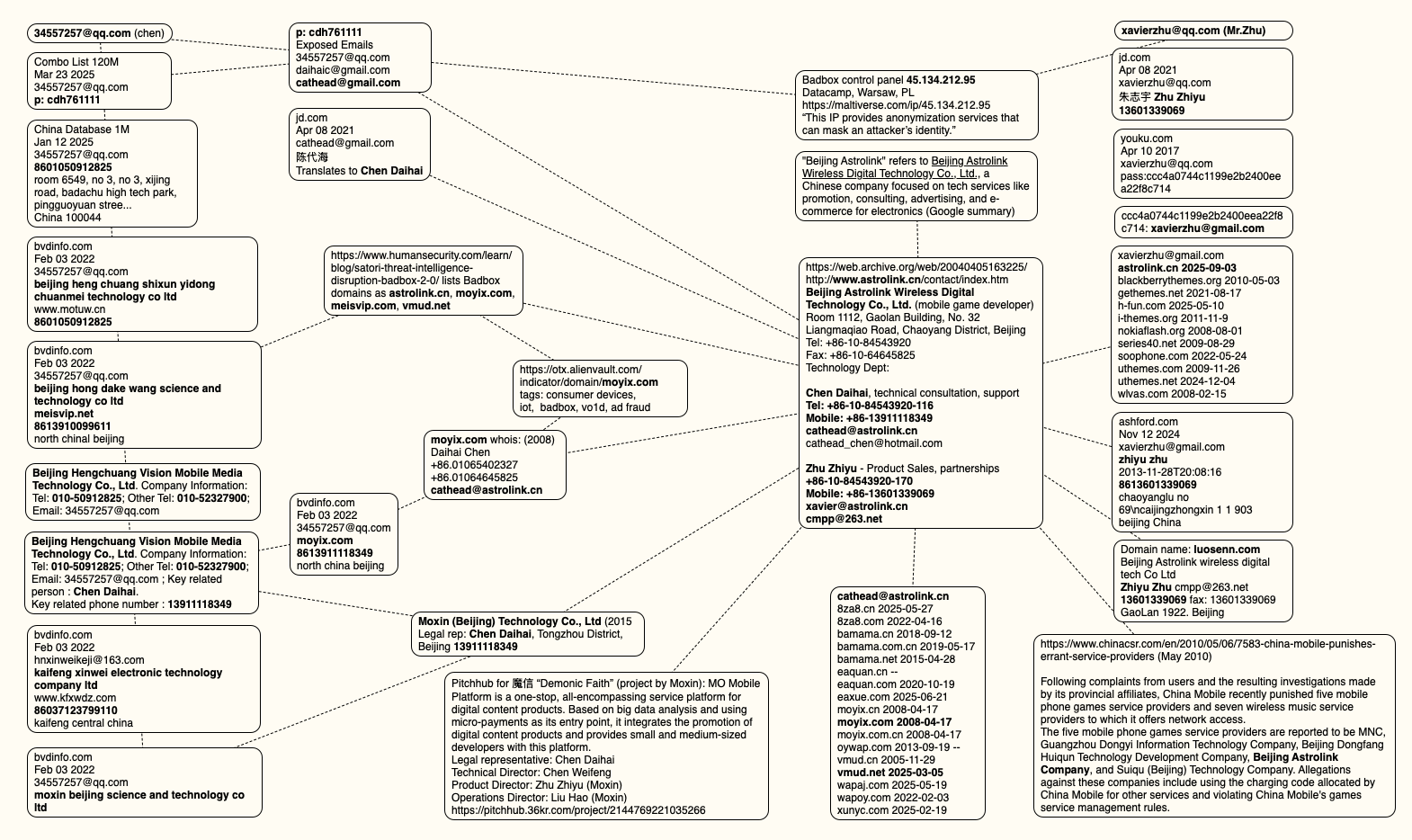
This mind map includes search pivots on the email addresses, company names and phone numbers that appear to connect Chen Daihai and Zhu Zhiyu to Badbox 2.0. Click to enlarge.
The idea that the Kimwolf botmasters could have direct access to the Badbox 2.0 botnet is a big deal, but explaining exactly why that is requires some background on how Kimwolf spreads to new devices. The botmasters figured out they could trick residential proxy services into relaying malicious commands to vulnerable devices behind the firewall on the unsuspecting user’s local network.
The vulnerable systems sought out by Kimwolf are primarily Internet of Things (IoT) devices like unsanctioned Android TV boxes and digital photo frames that have no discernible security or authentication built-in. Put simply, if you can communicate with these devices, you can compromise them with a single command.
Our January 2 story featured research from the proxy-tracking firm Synthient, which alerted 11 different residential proxy providers that their proxy endpoints were vulnerable to being abused for this kind of local network probing and exploitation.
Most of those vulnerable proxy providers have since taken steps to prevent customers from going upstream into the local networks of residential proxy endpoints, and it appeared that Kimwolf would no longer be able to quickly spread to millions of devices simply by exploiting some residential proxy provider.
However, the source of that Badbox 2.0 screenshot said the Kimwolf botmasters had an ace up their sleeve the whole time: Secret access to the Badbox 2.0 botnet control panel.
“Dort has gotten unauthorized access,” the source said. “So, what happened is normal proxy providers patched this. But Badbox doesn’t sell proxies by itself, so it’s not patched. And as long as Dort has access to Badbox, they would be able to load” the Kimwolf malware directly onto TV boxes associated with Badbox 2.0.
The source said it isn’t clear how Dort gained access to the Badbox botnet panel. But it’s unlikely that Dort’s existing account will persist for much longer: All of our notifications to the qq.com email addresses listed in the control panel screenshot received a copy of that image, as well as questions about the apparently rogue ABCD account.

From their original design as simple broadcast receivers, today’s televisions have evolved into powerful, internet-connected entertainment hubs. Combining traditional viewing with online capabilities, smart TVs provide instant access to streaming platforms, web browsing, voice assistants, and personalized recommendations.
As our TVs have grown smarter, however, they’ve also become gateways to new privacy and security challenges. In a chilling echo of George Orwell’s dystopian novel 1984, it’s possible that Big Brother, or in this case, Big Hacker, might be surveilling you through your own television.
In 2013, evidence emerged that smart TVs can be just as vulnerable to hacking as home computers, following an investigation by security analysts Aaron Grattafiori and Josh Yavor at iSEC Partners. Working with smart TV manufacturers to address potential vulnerabilities, the analysts presented their findings at the Black Hat network security conference in Las Vegas. Their demonstration highlighted the concerning possibility of smart TVs not only physically surveilling you through the built-in camera but also prying deeper into your personal life by collecting data on your web searches, app usage, and preferences.
Smart TVs can be hacked in several ways, but the gateway that opens your smart TV to these attacks is the IP address, which links with internet-driven apps such as Facebook and YouTube, as well as video streaming services, microphones, and even internal cameras. Because smart TVs often run the same code as computers and smartphones, such as JavaScript or HTML5, they are also susceptible to malware and spyware attacks. These are some of the ways your device can be hacked:
Once a hacker has compromised your smart TV, they can spy on you through several built-in technologies that collect data on your viewing habits, conversations, and online activities.
The key to managing these privacy risks is understanding what data your TV collects and taking control through privacy settings, network restrictions, and informed usage decisions.
Your smart TV data typically flows to multiple parties. It starts with the device manufacturer for product improvements, then to streaming app providers for content recommendations, on to advertising networks for targeted marketing, and analytics companies for usage insights. Recent regulatory guidance emphasizes that you should have clear visibility into these data-sharing relationships through your TV’s privacy policy.
You can limit data collection by disabling Automatic Content Recognition (ACR) in your TV’s privacy settings, turning off personalized advertising, and regularly reviewing app permissions. Consumer protection agencies require smart TV manufacturers to provide opt-out mechanisms for advertising personalization and data sharing with third parties.
Fortunately, you can significantly reduce your smart TV risks with some simple preventive measures:
Most smart TVs don’t fully turn off when you press the power button; they enter standby mode to enable quick startup. In this state, certain components may remain active and continue collecting data. It might maintain network connectivity to receive software updates, keep microphones and voice assistants ready to respond to wake words, or continue ACR that tracks your viewing habits.
To truly disconnect your TV from potential monitoring, you have several options:
It depends on your specific smart TV model and its manufacturing date. Most modern smart TVs manufactured after 2022 do not include built-in cameras. Major manufacturers such as Samsung, LG, Sony, and TCL have largely moved away from integrating cameras directly into their television sets due to privacy concerns and limited consumer adoption.
Some premium models and older smart TVs from 2018-2021 may still feature built-in cameras designed typically used for:
If your smart TV does have a camera, you still have control, as most smart TVs with cameras include physical privacy shutters, software controls to disable the camera, or the option to cover the lens. For external USB cameras, simply unplugging it ensures that no one can see you through the smart TV.
To determine if your smart TV has a camera, check the following:
If you discover your smart TV has a camera, you can take control of your privacy by disabling it in your TV’s settings, covering it with tape when not in use, or using any built-in privacy shutters.
Aside from the precautions listed above, there are other ways you can disable your smart TV’s camera:
If the thought of your living room turning into a hacker’s surveillance paradise sends a chill down your spine, you’re not alone. Fortunately, you can take some protective measures that keep your smart TV safe.
One of the best ways to protect yourself is to stay informed about the latest developments in smart TV security. Attend webinars, read articles, and follow experts in the field to stay current with the latest security threats and fixes.
Just as importantly, small but effective digital habits will also fortify your smart TV security: keep your TV’s firmware updated, stick to official app stores, secure your home Wi-Fi with strong encryption, use unique passwords for your devices, limit the use of social media and messaging apps on your TV, and be cautious about what you plug into your TV’s ports.
By following these recommendations, you can continue to relax in your living room and enjoy your digital entertainment experience without compromising your privacy and security.
The post How To Tell If Your Smart TV Spying on You appeared first on McAfee Blog.
Microsoft today pushed updates to fix at least 56 security flaws in its Windows operating systems and supported software. This final Patch Tuesday of 2025 tackles one zero-day bug that is already being exploited, as well as two publicly disclosed vulnerabilities.

Despite releasing a lower-than-normal number of security updates these past few months, Microsoft patched a whopping 1,129 vulnerabilities in 2025, an 11.9% increase from 2024. According to Satnam Narang at Tenable, this year marks the second consecutive year that Microsoft patched over one thousand vulnerabilities, and the third time it has done so since its inception.
The zero-day flaw patched today is CVE-2025-62221, a privilege escalation vulnerability affecting Windows 10 and later editions. The weakness resides in a component called the “Windows Cloud Files Mini Filter Driver” — a system driver that enables cloud applications to access file system functionalities.
“This is particularly concerning, as the mini filter is integral to services like OneDrive, Google Drive, and iCloud, and remains a core Windows component, even if none of those apps were installed,” said Adam Barnett, lead software engineer at Rapid7.
Only three of the flaws patched today earned Microsoft’s most-dire “critical” rating: Both CVE-2025-62554 and CVE-2025-62557 involve Microsoft Office, and both can exploited merely by viewing a booby-trapped email message in the Preview Pane. Another critical bug — CVE-2025-62562 — involves Microsoft Outlook, although Redmond says the Preview Pane is not an attack vector with this one.
But according to Microsoft, the vulnerabilities most likely to be exploited from this month’s patch batch are other (non-critical) privilege escalation bugs, including:
–CVE-2025-62458 — Win32k
–CVE-2025-62470 — Windows Common Log File System Driver
–CVE-2025-62472 — Windows Remote Access Connection Manager
–CVE-2025-59516 — Windows Storage VSP Driver
–CVE-2025-59517 — Windows Storage VSP Driver
Kev Breen, senior director of threat research at Immersive, said privilege escalation flaws are observed in almost every incident involving host compromises.
“We don’t know why Microsoft has marked these specifically as more likely, but the majority of these components have historically been exploited in the wild or have enough technical detail on previous CVEs that it would be easier for threat actors to weaponize these,” Breen said. “Either way, while not actively being exploited, these should be patched sooner rather than later.”
One of the more interesting vulnerabilities patched this month is CVE-2025-64671, a remote code execution flaw in the Github Copilot Plugin for Jetbrains AI-based coding assistant that is used by Microsoft and GitHub. Breen said this flaw would allow attackers to execute arbitrary code by tricking the large language model (LLM) into running commands that bypass the user’s “auto-approve” settings.
CVE-2025-64671 is part of a broader, more systemic security crisis that security researcher Ari Marzuk has branded IDEsaster (IDE stands for “integrated development environment”), which encompasses more than 30 separate vulnerabilities reported in nearly a dozen market-leading AI coding platforms, including Cursor, Windsurf, Gemini CLI, and Claude Code.
The other publicly-disclosed vulnerability patched today is CVE-2025-54100, a remote code execution bug in Windows Powershell on Windows Server 2008 and later that allows an unauthenticated attacker to run code in the security context of the user.
For anyone seeking a more granular breakdown of the security updates Microsoft pushed today, check out the roundup at the SANS Internet Storm Center. As always, please leave a note in the comments if you experience problems applying any of this month’s Windows patches.
A prolific cybercriminal group that calls itself “Scattered LAPSUS$ Hunters” has dominated headlines this year by regularly stealing data from and publicly mass extorting dozens of major corporations. But the tables seem to have turned somewhat for “Rey,” the moniker chosen by the technical operator and public face of the hacker group: Earlier this week, Rey confirmed his real life identity and agreed to an interview after KrebsOnSecurity tracked him down and contacted his father.
Scattered LAPSUS$ Hunters (SLSH) is thought to be an amalgamation of three hacking groups — Scattered Spider, LAPSUS$ and ShinyHunters. Members of these gangs hail from many of the same chat channels on the Com, a mostly English-language cybercriminal community that operates across an ocean of Telegram and Discord servers.
In May 2025, SLSH members launched a social engineering campaign that used voice phishing to trick targets into connecting a malicious app to their organization’s Salesforce portal. The group later launched a data leak portal that threatened to publish the internal data of three dozen companies that allegedly had Salesforce data stolen, including Toyota, FedEx, Disney/Hulu, and UPS.
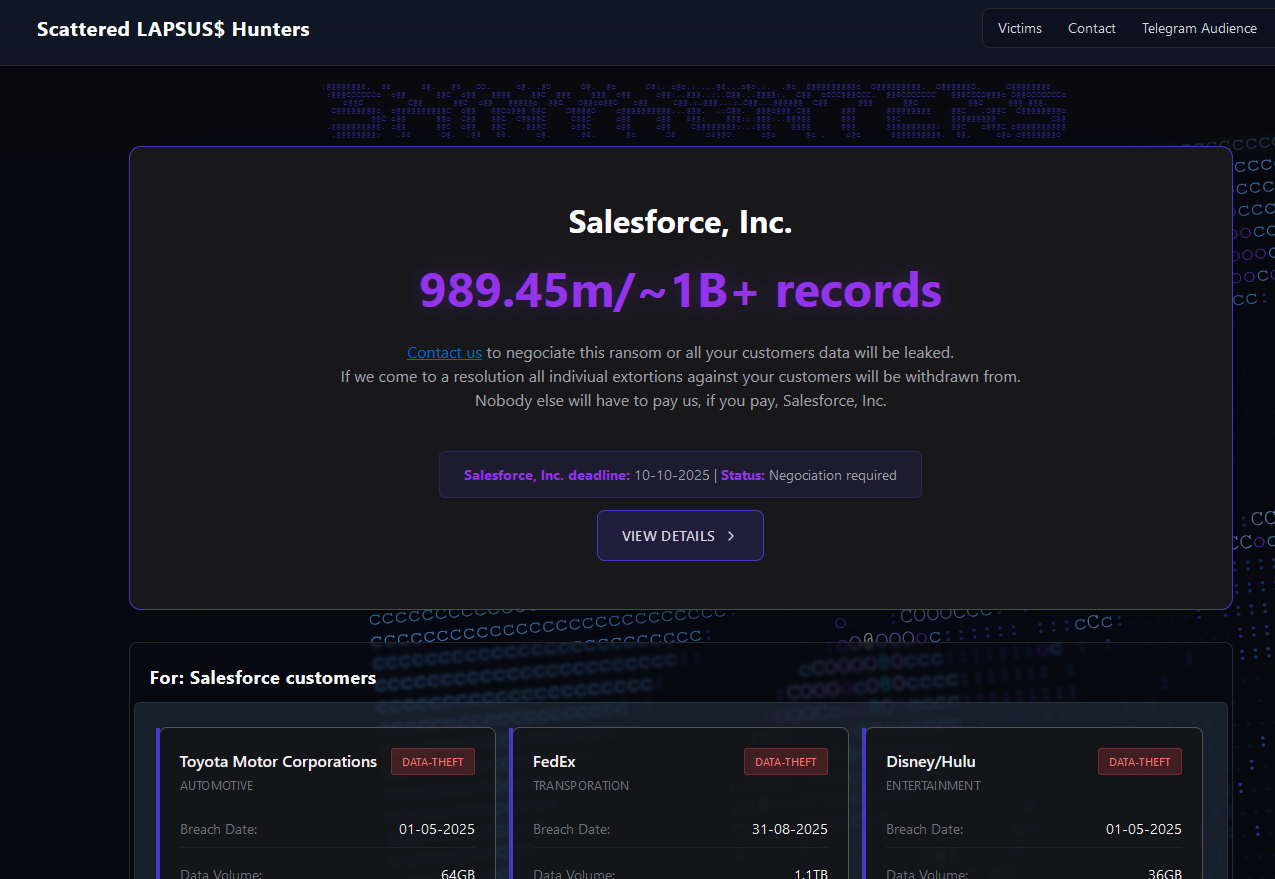
The new extortion website tied to ShinyHunters, which threatens to publish stolen data unless Salesforce or individual victim companies agree to pay a ransom.
Last week, the SLSH Telegram channel featured an offer to recruit and reward “insiders,” employees at large companies who agree to share internal access to their employer’s network for a share of whatever ransom payment is ultimately paid by the victim company.
SLSH has solicited insider access previously, but their latest call for disgruntled employees started making the rounds on social media at the same time news broke that the cybersecurity firm Crowdstrike had fired an employee for allegedly sharing screenshots of internal systems with the hacker group (Crowdstrike said their systems were never compromised and that it has turned the matter over to law enforcement agencies).
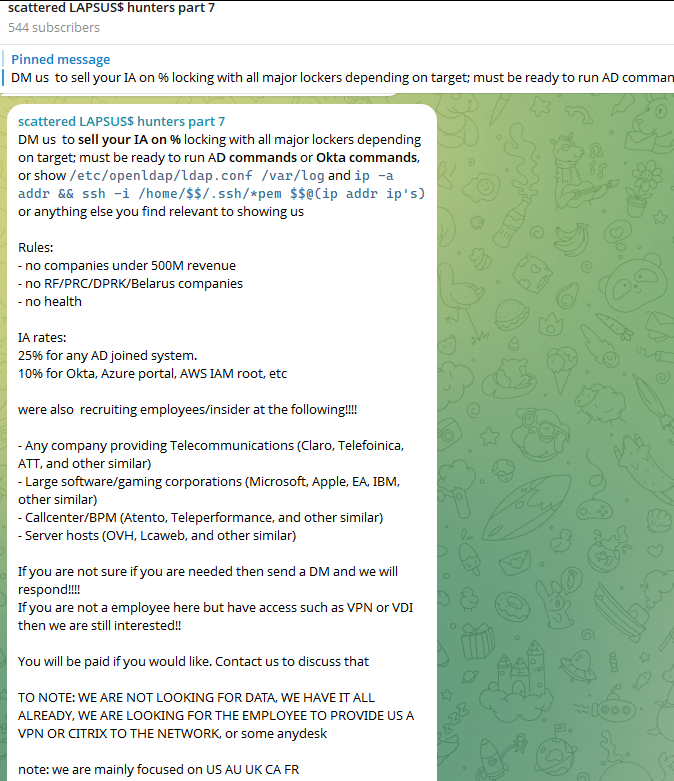
The Telegram server for the Scattered LAPSUS$ Hunters has been attempting to recruit insiders at large companies.
Members of SLSH have traditionally used other ransomware gangs’ encryptors in attacks, including malware from ransomware affiliate programs like ALPHV/BlackCat, Qilin, RansomHub, and DragonForce. But last week, SLSH announced on its Telegram channel the release of their own ransomware-as-a-service operation called ShinySp1d3r.
The individual responsible for releasing the ShinySp1d3r ransomware offering is a core SLSH member who goes by the handle “Rey” and who is currently one of just three administrators of the SLSH Telegram channel. Previously, Rey was an administrator of the data leak website for Hellcat, a ransomware group that surfaced in late 2024 and was involved in attacks on companies including Schneider Electric, Telefonica, and Orange Romania.
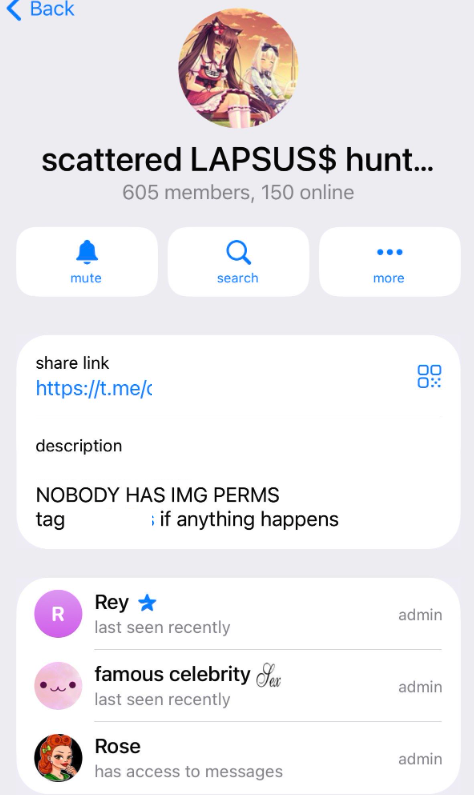
A recent, slightly redacted screenshot of the Scattered LAPSUS$ Hunters Telegram channel description, showing Rey as one of three administrators.
Also in 2024, Rey would take over as administrator of the most recent incarnation of BreachForums, an English-language cybercrime forum whose domain names have been seized on multiple occasions by the FBI and/or by international authorities. In April 2025, Rey posted on Twitter/X about another FBI seizure of BreachForums.
On October 5, 2025, the FBI announced it had once again seized the domains associated with BreachForums, which it described as a major criminal marketplace used by ShinyHunters and others to traffic in stolen data and facilitate extortion.
“This takedown removes access to a key hub used by these actors to monetize intrusions, recruit collaborators, and target victims across multiple sectors,” the FBI said.
Incredibly, Rey would make a series of critical operational security mistakes last year that provided multiple avenues to ascertain and confirm his real-life identity and location. Read on to learn how it all unraveled for Rey.
According to the cyber intelligence firm Intel 471, Rey was an active user on various BreachForums reincarnations over the past two years, authoring more than 200 posts between February 2024 and July 2025. Intel 471 says Rey previously used the handle “Hikki-Chan” on BreachForums, where their first post shared data allegedly stolen from the U.S. Centers for Disease Control and Prevention (CDC).
In that February 2024 post about the CDC, Hikki-Chan says they could be reached at the Telegram username @wristmug. In May 2024, @wristmug posted in a Telegram group chat called “Pantifan” a copy of an extortion email they said they received that included their email address and password.
The message that @wristmug cut and pasted appears to have been part of an automated email scam that claims it was sent by a hacker who has compromised your computer and used your webcam to record a video of you while you were watching porn. These missives threaten to release the video to all your contacts unless you pay a Bitcoin ransom, and they typically reference a real password the recipient has used previously.
“Noooooo,” the @wristmug account wrote in mock horror after posting a screenshot of the scam message. “I must be done guys.”
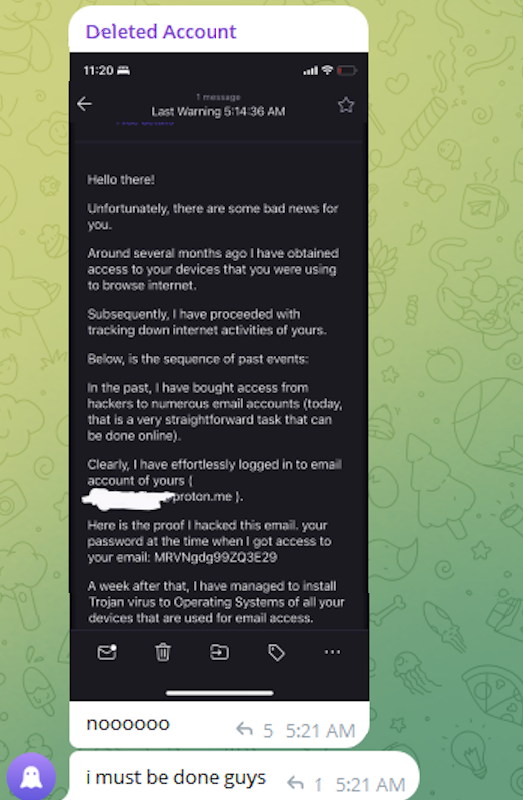
A message posted to Telegram by Rey/@wristmug.
In posting their screenshot, @wristmug redacted the username portion of the email address referenced in the body of the scam message. However, they did not redact their previously-used password, and they left the domain portion of their email address (@proton.me) visible in the screenshot.
Searching on @wristmug’s rather unique 15-character password in the breach tracking service Spycloud finds it is known to have been used by just one email address: cybero5tdev@proton.me. According to Spycloud, those credentials were exposed at least twice in early 2024 when this user’s device was infected with an infostealer trojan that siphoned all of its stored usernames, passwords and authentication cookies (a finding that was initially revealed in March 2025 by the cyber intelligence firm KELA).
Intel 471 shows the email address cybero5tdev@proton.me belonged to a BreachForums member who went by the username o5tdev. Searching on this nickname in Google brings up at least two website defacement archives showing that a user named o5tdev was previously involved in defacing sites with pro-Palestinian messages. The screenshot below, for example, shows that 05tdev was part of a group called Cyb3r Drag0nz Team.

Rey/o5tdev’s defacement pages. Image: archive.org.
A 2023 report from SentinelOne described Cyb3r Drag0nz Team as a hacktivist group with a history of launching DDoS attacks and cyber defacements as well as engaging in data leak activity.
“Cyb3r Drag0nz Team claims to have leaked data on over a million of Israeli citizens spread across multiple leaks,” SentinelOne reported. “To date, the group has released multiple .RAR archives of purported personal information on citizens across Israel.”
The cyber intelligence firm Flashpoint finds the Telegram user @05tdev was active in 2023 and early 2024, posting in Arabic on anti-Israel channels like “Ghost of Palestine” [full disclosure: Flashpoint is currently an advertiser on this blog].
Flashpoint shows that Rey’s Telegram account (ID7047194296) was particularly active in a cybercrime-focused channel called Jacuzzi, where this user shared several personal details, including that their father was an airline pilot. Rey claimed in 2024 to be 15 years old, and to have family connections to Ireland.
Specifically, Rey mentioned in several Telegram chats that he had Irish heritage, even posting a graphic that shows the prevalence of the surname “Ginty.”
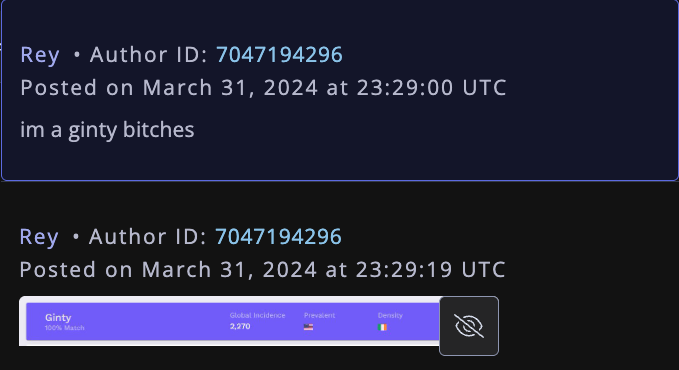
Rey, on Telegram claiming to have association to the surname “Ginty.” Image: Flashpoint.
Spycloud indexed hundreds of credentials stolen from cybero5dev@proton.me, and those details indicate that Rey’s computer is a shared Microsoft Windows device located in Amman, Jordan. The credential data stolen from Rey in early 2024 show there are multiple users of the infected PC, but that all shared the same last name of Khader and an address in Amman, Jordan.
The “autofill” data lifted from Rey’s family PC contains an entry for a 46-year-old Zaid Khader that says his mother’s maiden name was Ginty. The infostealer data also shows Zaid Khader frequently accessed internal websites for employees of Royal Jordanian Airlines.
The infostealer data makes clear that Rey’s full name is Saif Al-Din Khader. Having no luck contacting Saif directly, KrebsOnSecurity sent an email to his father Zaid. The message invited the father to respond via email, phone or Signal, explaining that his son appeared to be deeply enmeshed in a serious cybercrime conspiracy.
Less than two hours later, I received a Signal message from Saif, who said his dad suspected the email was a scam and had forwarded it to him.
“I saw your email, unfortunately I don’t think my dad would respond to this because they think its some ‘scam email,'” said Saif, who told me he turns 16 years old next month. “So I decided to talk to you directly.”
Saif explained that he’d already heard from European law enforcement officials, and had been trying to extricate himself from SLSH. When asked why then he was involved in releasing SLSH’s new ShinySp1d3r ransomware-as-a-service offering, Saif said he couldn’t just suddenly quit the group.
“Well I cant just dip like that, I’m trying to clean up everything I’m associated with and move on,” he said.

The former Hellcat ransomware site. Image: Kelacyber.com
He also shared that ShinySp1d3r is just a rehash of Hellcat ransomware, except modified with AI tools. “I gave the source code of Hellcat ransomware out basically.”
Saif claims he reached out on his own recently to the Telegram account for Operation Endgame, the codename for an ongoing law enforcement operation targeting cybercrime services, vendors and their customers.
“I’m already cooperating with law enforcement,” Saif said. “In fact, I have been talking to them since at least June. I have told them nearly everything. I haven’t really done anything like breaching into a corp or extortion related since September.”
Saif suggested that a story about him right now could endanger any further cooperation he may be able to provide. He also said he wasn’t sure if the U.S. or European authorities had been in contact with the Jordanian government about his involvement with the hacking group.
“A story would bring so much unwanted heat and would make things very difficult if I’m going to cooperate,” Saif said. “I’m unsure whats going to happen they said they’re in contact with multiple countries regarding my request but its been like an entire week and I got no updates from them.”
Saif shared a screenshot that indicated he’d contacted Europol authorities late last month. But he couldn’t name any law enforcement officials he said were responding to his inquiries, and KrebsOnSecurity was unable to verify his claims.
“I don’t really care I just want to move on from all this stuff even if its going to be prison time or whatever they gonna say,” Saif said.
An intermittent outage at Cloudflare on Tuesday briefly knocked many of the Internet’s top destinations offline. Some affected Cloudflare customers were able to pivot away from the platform temporarily so that visitors could still access their websites. But security experts say doing so may have also triggered an impromptu network penetration test for organizations that have come to rely on Cloudflare to block many types of abusive and malicious traffic.
At around 6:30 EST/11:30 UTC on Nov. 18, Cloudflare’s status page acknowledged the company was experiencing “an internal service degradation.” After several hours of Cloudflare services coming back up and failing again, many websites behind Cloudflare found they could not migrate away from using the company’s services because the Cloudflare portal was unreachable and/or because they also were getting their domain name system (DNS) services from Cloudflare.
However, some customers did manage to pivot their domains away from Cloudflare during the outage. And many of those organizations probably need to take a closer look at their web application firewall (WAF) logs during that time, said Aaron Turner, a faculty member at IANS Research.
Turner said Cloudflare’s WAF does a good job filtering out malicious traffic that matches any one of the top ten types of application-layer attacks, including credential stuffing, cross-site scripting, SQL injection, bot attacks and API abuse. But he said this outage might be a good opportunity for Cloudflare customers to better understand how their own app and website defenses may be failing without Cloudflare’s help.
“Your developers could have been lazy in the past for SQL injection because Cloudflare stopped that stuff at the edge,” Turner said. “Maybe you didn’t have the best security QA [quality assurance] for certain things because Cloudflare was the control layer to compensate for that.”
Turner said one company he’s working with saw a huge increase in log volume and they are still trying to figure out what was “legit malicious” versus just noise.
“It looks like there was about an eight hour window when several high-profile sites decided to bypass Cloudflare for the sake of availability,” Turner said. “Many companies have essentially relied on Cloudflare for the OWASP Top Ten [web application vulnerabilities] and a whole range of bot blocking. How much badness could have happened in that window? Any organization that made that decision needs to look closely at any exposed infrastructure to see if they have someone persisting after they’ve switched back to Cloudflare protections.”
Turner said some cybercrime groups likely noticed when an online merchant they normally stalk stopped using Cloudflare’s services during the outage.
“Let’s say you were an attacker, trying to grind your way into a target, but you felt that Cloudflare was in the way in the past,” he said. “Then you see through DNS changes that the target has eliminated Cloudflare from their web stack due to the outage. You’re now going to launch a whole bunch of new attacks because the protective layer is no longer in place.”
Nicole Scott, senior product marketing manager at the McLean, Va. based Replica Cyber, called yesterday’s outage “a free tabletop exercise, whether you meant to run one or not.”
“That few-hour window was a live stress test of how your organization routes around its own control plane and shadow IT blossoms under the sunlamp of time pressure,” Scott said in a post on LinkedIn. “Yes, look at the traffic that hit you while protections were weakened. But also look hard at the behavior inside your org.”
Scott said organizations seeking security insights from the Cloudflare outage should ask themselves:
1. What was turned off or bypassed (WAF, bot protections, geo blocks), and for how long?
2. What emergency DNS or routing changes were made, and who approved them?
3. Did people shift work to personal devices, home Wi-Fi, or unsanctioned Software-as-a-Service providers to get around the outage?
4. Did anyone stand up new services, tunnels, or vendor accounts “just for now”?
5. Is there a plan to unwind those changes, or are they now permanent workarounds?
6. For the next incident, what’s the intentional fallback plan, instead of decentralized improvisation?
In a postmortem published Tuesday evening, Cloudflare said the disruption was not caused, directly or indirectly, by a cyberattack or malicious activity of any kind.
“Instead, it was triggered by a change to one of our database systems’ permissions which caused the database to output multiple entries into a ‘feature file’ used by our Bot Management system,” Cloudflare CEO Matthew Prince wrote. “That feature file, in turn, doubled in size. The larger-than-expected feature file was then propagated to all the machines that make up our network.”
Cloudflare estimates that roughly 20 percent of websites use its services, and with much of the modern web relying heavily on a handful of other cloud providers including AWS and Azure, even a brief outage at one of these platforms can create a single point of failure for many organizations.
Martin Greenfield, CEO at the IT consultancy Quod Orbis, said Tuesday’s outage was another reminder that many organizations may be putting too many of their eggs in one basket.
“There are several practical and overdue fixes,” Greenfield advised. “Split your estate. Spread WAF and DDoS protection across multiple zones. Use multi-vendor DNS. Segment applications so a single provider outage doesn’t cascade. And continuously monitor controls to detect single-vendor dependency.”
For the past week, domains associated with the massive Aisuru botnet have repeatedly usurped Amazon, Apple, Google and Microsoft in Cloudflare’s public ranking of the most frequently requested websites. Cloudflare responded by redacting Aisuru domain names from their top websites list. The chief executive at Cloudflare says Aisuru’s overlords are using the botnet to boost their malicious domain rankings, while simultaneously attacking the company’s domain name system (DNS) service.
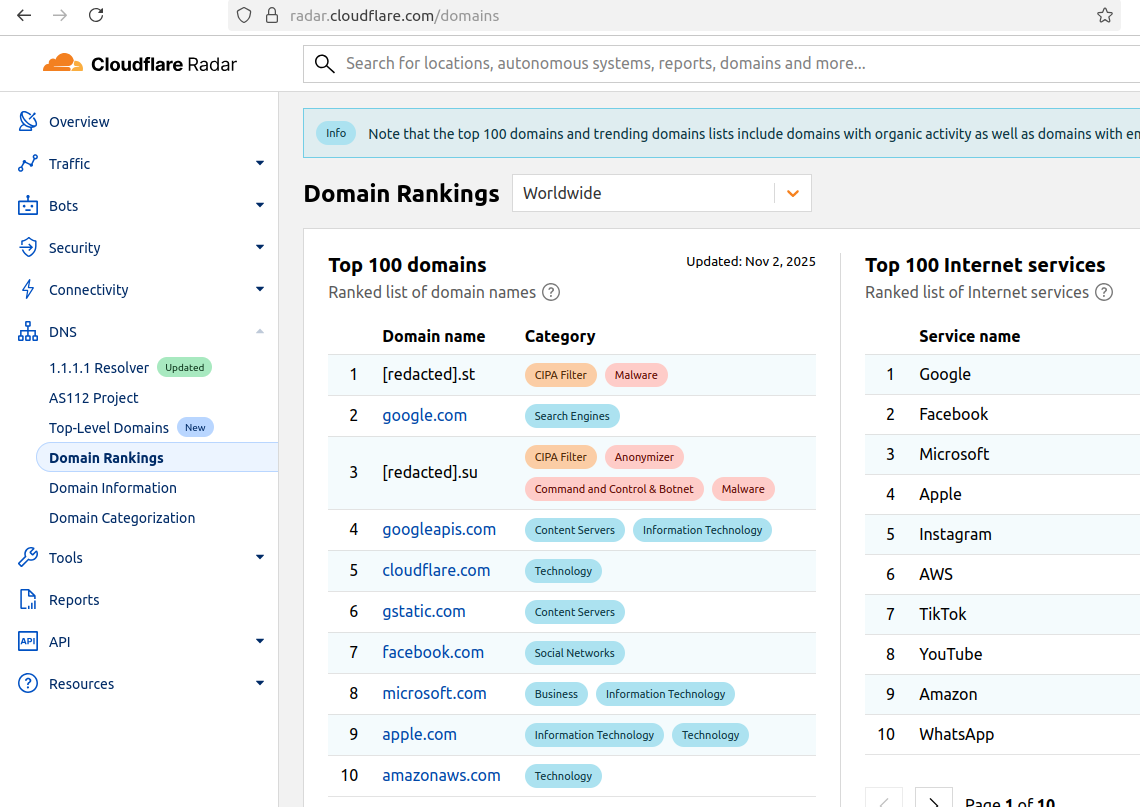
The #1 and #3 positions in this chart are Aisuru botnet controllers with their full domain names redacted. Source: radar.cloudflare.com.
Aisuru is a rapidly growing botnet comprising hundreds of thousands of hacked Internet of Things (IoT) devices, such as poorly secured Internet routers and security cameras. The botnet has increased in size and firepower significantly since its debut in 2024, demonstrating the ability to launch record distributed denial-of-service (DDoS) attacks nearing 30 terabits of data per second.
Until recently, Aisuru’s malicious code instructed all infected systems to use DNS servers from Google — specifically, the servers at 8.8.8.8. But in early October, Aisuru switched to invoking Cloudflare’s main DNS server — 1.1.1.1 — and over the past week domains used by Aisuru to control infected systems started populating Cloudflare’s top domain rankings.
As screenshots of Aisuru domains claiming two of the Top 10 positions ping-ponged across social media, many feared this was yet another sign that an already untamable botnet was running completely amok. One Aisuru botnet domain that sat prominently for days at #1 on the list was someone’s street address in Massachusetts followed by “.com”. Other Aisuru domains mimicked those belonging to major cloud providers.
Cloudflare tried to address these security, brand confusion and privacy concerns by partially redacting the malicious domains, and adding a warning at the top of its rankings:
“Note that the top 100 domains and trending domains lists include domains with organic activity as well as domains with emerging malicious behavior.”
Cloudflare CEO Matthew Prince told KrebsOnSecurity the company’s domain ranking system is fairly simplistic, and that it merely measures the volume of DNS queries to 1.1.1.1.
“The attacker is just generating a ton of requests, maybe to influence the ranking but also to attack our DNS service,” Prince said, adding that Cloudflare has heard reports of other large public DNS services seeing similar uptick in attacks. “We’re fixing the ranking to make it smarter. And, in the meantime, redacting any sites we classify as malware.”
Renee Burton, vice president of threat intel at the DNS security firm Infoblox, said many people erroneously assumed that the skewed Cloudflare domain rankings meant there were more bot-infected devices than there were regular devices querying sites like Google and Apple and Microsoft.
“Cloudflare’s documentation is clear — they know that when it comes to ranking domains you have to make choices on how to normalize things,” Burton wrote on LinkedIn. “There are many aspects that are simply out of your control. Why is it hard? Because reasons. TTL values, caching, prefetching, architecture, load balancing. Things that have shared control between the domain owner and everything in between.”
Alex Greenland is CEO of the anti-phishing and security firm Epi. Greenland said he understands the technical reason why Aisuru botnet domains are showing up in Cloudflare’s rankings (those rankings are based on DNS query volume, not actual web visits). But he said they’re still not meant to be there.
“It’s a failure on Cloudflare’s part, and reveals a compromise of the trust and integrity of their rankings,” he said.
Greenland said Cloudflare planned for its Domain Rankings to list the most popular domains as used by human users, and it was never meant to be a raw calculation of query frequency or traffic volume going through their 1.1.1.1 DNS resolver.
“They spelled out how their popularity algorithm is designed to reflect real human use and exclude automated traffic (they said they’re good at this),” Greenland wrote on LinkedIn. “So something has evidently gone wrong internally. We should have two rankings: one representing trust and real human use, and another derived from raw DNS volume.”
Why might it be a good idea to wholly separate malicious domains from the list? Greenland notes that Cloudflare Domain Rankings see widespread use for trust and safety determination, by browsers, DNS resolvers, safe browsing APIs and things like TRANCO.
“TRANCO is a respected open source list of the top million domains, and Cloudflare Radar is one of their five data providers,” he continued. “So there can be serious knock-on effects when a malicious domain features in Cloudflare’s top 10/100/1000/million. To many people and systems, the top 10 and 100 are naively considered safe and trusted, even though algorithmically-defined top-N lists will always be somewhat crude.”
Over this past week, Cloudflare started redacting portions of the malicious Aisuru domains from its Top Domains list, leaving only their domain suffix visible. Sometime in the past 24 hours, Cloudflare appears to have begun hiding the malicious Aisuru domains entirely from the web version of that list. However, downloading a spreadsheet of the current Top 200 domains from Cloudflare Radar shows an Aisuru domain still at the very top.
According to Cloudflare’s website, the majority of DNS queries to the top Aisuru domains — nearly 52 percent — originated from the United States. This tracks with my reporting from early October, which found Aisuru was drawing most of its firepower from IoT devices hosted on U.S. Internet providers like AT&T, Comcast and Verizon.
Experts tracking Aisuru say the botnet relies on well more than a hundred control servers, and that for the moment at least most of those domains are registered in the .su top-level domain (TLD). Dot-su is the TLD assigned to the former Soviet Union (.su’s Wikipedia page says the TLD was created just 15 months before the fall of the Berlin wall).
A Cloudflare blog post from October 27 found that .su had the highest “DNS magnitude” of any TLD, referring to a metric estimating the popularity of a TLD based on the number of unique networks querying Cloudflare’s 1.1.1.1 resolver. The report concluded that the top .su hostnames were associated with a popular online world-building game, and that more than half of the queries for that TLD came from the United States, Brazil and Germany [it’s worth noting that servers for the world-building game Minecraft were some of Aisuru’s most frequent targets].
A simple and crude way to detect Aisuru bot activity on a network may be to set an alert on any systems attempting to contact domains ending in .su. This TLD is frequently abused for cybercrime and by cybercrime forums and services, and blocking access to it entirely is unlikely to raise any legitimate complaints.
KrebsOnSecurity last week was hit by a near record distributed denial-of-service (DDoS) attack that clocked in at more than 6.3 terabits of data per second (a terabit is one trillion bits of data). The brief attack appears to have been a test run for a massive new Internet of Things (IoT) botnet capable of launching crippling digital assaults that few web destinations can withstand. Read on for more about the botnet, the attack, and the apparent creator of this global menace.

For reference, the 6.3 Tbps attack last week was ten times the size of the assault launched against this site in 2016 by the Mirai IoT botnet, which held KrebsOnSecurity offline for nearly four days. The 2016 assault was so large that Akamai – which was providing pro-bono DDoS protection for KrebsOnSecurity at the time — asked me to leave their service because the attack was causing problems for their paying customers.
Since the Mirai attack, KrebsOnSecurity.com has been behind the protection of Project Shield, a free DDoS defense service that Google provides to websites offering news, human rights, and election-related content. Google Security Engineer Damian Menscher told KrebsOnSecurity the May 12 attack was the largest Google has ever handled. In terms of sheer size, it is second only to a very similar attack that Cloudflare mitigated and wrote about in April.
After comparing notes with Cloudflare, Menscher said the botnet that launched both attacks bears the fingerprints of Aisuru, a digital siege machine that first surfaced less than a year ago. Menscher said the attack on KrebsOnSecurity lasted less than a minute, hurling large UDP data packets at random ports at a rate of approximately 585 million data packets per second.
“It was the type of attack normally designed to overwhelm network links,” Menscher said, referring to the throughput connections between and among various Internet service providers (ISPs). “For most companies, this size of attack would kill them.”
The Aisuru botnet comprises a globally-dispersed collection of hacked IoT devices, including routers, digital video recorders and other systems that are commandeered via default passwords or software vulnerabilities. As documented by researchers at QiAnXin XLab, the botnet was first identified in an August 2024 attack on a large gaming platform.
Aisuru reportedly went quiet after that exposure, only to reappear in November with even more firepower and software exploits. In a January 2025 report, XLab found the new and improved Aisuru (a.k.a. “Airashi“) had incorporated a previously unknown zero-day vulnerability in Cambium Networks cnPilot routers.
The people behind the Aisuru botnet have been peddling access to their DDoS machine in public Telegram chat channels that are closely monitored by multiple security firms. In August 2024, the botnet was rented out in subscription tiers ranging from $150 per day to $600 per week, offering attacks of up to two terabits per second.
“You may not attack any measurement walls, healthcare facilities, schools or government sites,” read a notice posted on Telegram by the Aisuru botnet owners in August 2024.
Interested parties were told to contact the Telegram handle “@yfork” to purchase a subscription. The account @yfork previously used the nickname “Forky,” an identity that has been posting to public DDoS-focused Telegram channels since 2021.
According to the FBI, Forky’s DDoS-for-hire domains have been seized in multiple law enforcement operations over the years. Last year, Forky said on Telegram he was selling the domain stresser[.]best, which saw its servers seized by the FBI in 2022 as part of an ongoing international law enforcement effort aimed at diminishing the supply of and demand for DDoS-for-hire services.
“The operator of this service, who calls himself ‘Forky,’ operates a Telegram channel to advertise features and communicate with current and prospective DDoS customers,” reads an FBI seizure warrant (PDF) issued for stresser[.]best. The FBI warrant stated that on the same day the seizures were announced, Forky posted a link to a story on this blog that detailed the domain seizure operation, adding the comment, “We are buying our new domains right now.”
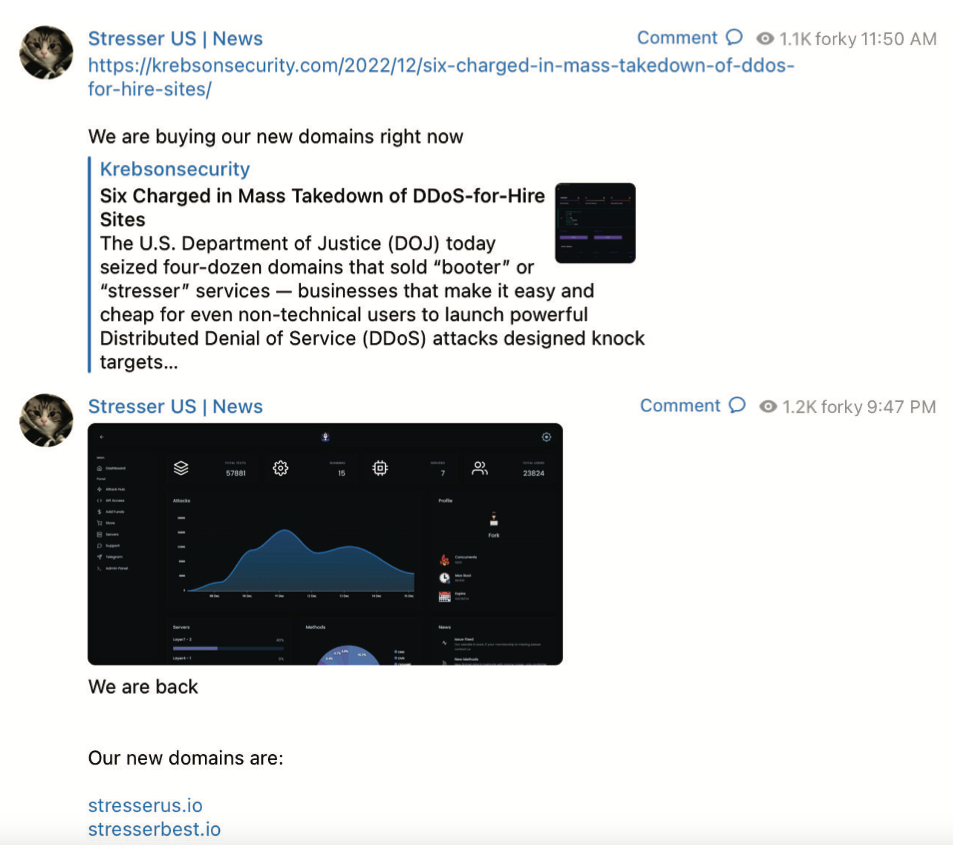
A screenshot from the FBI’s seizure warrant for Forky’s DDoS-for-hire domains shows Forky announcing the resurrection of their service at new domains.
Approximately ten hours later, Forky posted again, including a screenshot of the stresser[.]best user dashboard, instructing customers to use their saved passwords for the old website on the new one.
A review of Forky’s posts to public Telegram channels — as indexed by the cyber intelligence firms Unit 221B and Flashpoint — reveals a 21-year-old individual who claims to reside in Brazil [full disclosure: Flashpoint is currently an advertiser on this blog].
Since late 2022, Forky’s posts have frequently promoted a DDoS mitigation company and ISP that he operates called botshield[.]io. The Botshield website is connected to a business entity registered in the United Kingdom called Botshield LTD, which lists a 21-year-old woman from Sao Paulo, Brazil as the director. Internet routing records indicate Botshield (AS213613) currently controls several hundred Internet addresses that were allocated to the company earlier this year.
Domaintools.com reports that botshield[.]io was registered in July 2022 to a Kaike Southier Leite in Sao Paulo. A LinkedIn profile by the same name says this individual is a network specialist from Brazil who works in “the planning and implementation of robust network infrastructures, with a focus on security, DDoS mitigation, colocation and cloud server services.”

Image: Jaclyn Vernace / Shutterstock.com.
In his posts to public Telegram chat channels, Forky has hardly attempted to conceal his whereabouts or identity. In countless chat conversations indexed by Unit 221B, Forky could be seen talking about everyday life in Brazil, often remarking on the extremely low or high prices in Brazil for a range of goods, from computer and networking gear to narcotics and food.
Reached via Telegram, Forky claimed he was “not involved in this type of illegal actions for years now,” and that the project had been taken over by other unspecified developers. Forky initially told KrebsOnSecurity he had been out of the botnet scene for years, only to concede this wasn’t true when presented with public posts on Telegram from late last year that clearly showed otherwise.
Forky denied being involved in the attack on KrebsOnSecurity, but acknowledged that he helped to develop and market the Aisuru botnet. Forky claims he is now merely a staff member for the Aisuru botnet team, and that he stopped running the botnet roughly two months ago after starting a family. Forky also said the woman named as director of Botshield is related to him.
Forky offered equivocal, evasive responses to a number of questions about the Aisuru botnet and his business endeavors. But on one point he was crystal clear:
“I have zero fear about you, the FBI, or Interpol,” Forky said, asserting that he is now almost entirely focused on their hosting business — Botshield.
Forky declined to discuss the makeup of his ISP’s clientele, or to clarify whether Botshield was more of a hosting provider or a DDoS mitigation firm. However, Forky has posted on Telegram about Botshield successfully mitigating large DDoS attacks launched against other DDoS-for-hire services.
DomainTools finds the same Sao Paulo street address in the registration records for botshield[.]io was used to register several other domains, including cant-mitigate[.]us. The email address in the WHOIS records for that domain is forkcontato@gmail.com, which DomainTools says was used to register the domain for the now-defunct DDoS-for-hire service stresser[.]us, one of the domains seized in the FBI’s 2023 crackdown.
On May 8, 2023, the U.S. Department of Justice announced the seizure of stresser[.]us, along with a dozen other domains offering DDoS services. The DOJ said ten of the 13 domains were reincarnations of services that were seized during a prior sweep in December, which targeted 48 top stresser services (also known as “booters”).
Forky claimed he could find out who attacked my site with Aisuru. But when pressed a day later on the question, Forky said he’d come up empty-handed.
“I tried to ask around, all the big guys are not retarded enough to attack you,” Forky explained in an interview on Telegram. “I didn’t have anything to do with it. But you are welcome to write the story and try to put the blame on me.”
The 6.3 Tbps attack last week caused no visible disruption to this site, in part because it was so brief — lasting approximately 45 seconds. DDoS attacks of such magnitude and brevity typically are produced when botnet operators wish to test or demonstrate their firepower for the benefit of potential buyers. Indeed, Google’s Menscher said it is likely that both the May 12 attack and the slightly larger 6.5 Tbps attack against Cloudflare last month were simply tests of the same botnet’s capabilities.
In many ways, the threat posed by the Aisuru/Airashi botnet is reminiscent of Mirai, an innovative IoT malware strain that emerged in the summer of 2016 and successfully out-competed virtually all other IoT malware strains in existence at the time.
As first revealed by KrebsOnSecurity in January 2017, the Mirai authors were two U.S. men who co-ran a DDoS mitigation service — even as they were selling far more lucrative DDoS-for-hire services using the most powerful botnet on the planet.
Less than a week after the Mirai botnet was used in a days-long DDoS against KrebsOnSecurity, the Mirai authors published the source code to their botnet so that they would not be the only ones in possession of it in the event of their arrest by federal investigators.
Ironically, the leaking of the Mirai source is precisely what led to the eventual unmasking and arrest of the Mirai authors, who went on to serve probation sentences that required them to consult with FBI investigators on DDoS investigations. But that leak also rapidly led to the creation of dozens of Mirai botnet clones, many of which were harnessed to fuel their own powerful DDoS-for-hire services.
Menscher told KrebsOnSecurity that as counterintuitive as it may sound, the Internet as a whole would probably be better off if the source code for Aisuru became public knowledge. After all, he said, the people behind Aisuru are in constant competition with other IoT botnet operators who are all striving to commandeer a finite number of vulnerable IoT devices globally.
Such a development would almost certainly cause a proliferation of Aisuru botnet clones, he said, but at least then the overall firepower from each individual botnet would be greatly diminished — or at least within range of the mitigation capabilities of most DDoS protection providers.
Barring a source code leak, Menscher said, it would be nice if someone published the full list of software exploits being used by the Aisuru operators to grow their botnet so quickly.
“Part of the reason Mirai was so dangerous was that it effectively took out competing botnets,” he said. “This attack somehow managed to compromise all these boxes that nobody else knows about. Ideally, we’d want to see that fragmented out, so that no [individual botnet operator] controls too much.”
This GitHub repository provides a range of search queries, known as "dorks," for Shodan, a powerful tool used to search for Internet-connected devices. The dorks are designed to help security researchers discover potential vulnerabilities and configuration issues in various types of devices such as webcams, routers, and servers. This resource is helpful for those interested in exploring network security and conducting vulnerability scanning, including both beginners and experienced information security professionals. By leveraging this repository, users can improve the security of their own networks and protect against potential attacks.
aa3939fc357723135870d5036b12a67097b03309
app="HIKVISION-综合安防管理平台"
"AppleHttpServer"
"AutobahnPython"
basic realm="Kettle"
Bullwark
cassandra
Chromecast
"ClickShareSession"
"/config/log_off_page.htm"
'"connection: upgrade"'
"cowboy"
cpe:"cpe:2.3:a:apache:cassandra"
cpe:"cpe:2.3:a:backdropcms:backdrop"
cpe:"cpe:2.3:a:bolt:bolt"
cpe:"cpe:2.3:a:cisco:sd-wan"
cpe:"cpe:2.3:a:ckeditor:ckeditor"
cpe:"cpe:2.3:a:cmsimple:cmsimple"
cpe:"cpe:2.3:a:djangoproject:django"
cpe:"cpe:2.3:a:djangoproject:django" || http.title:"Django administration"
cpe:"cpe:2.3:a:eclipse:jetty"
cpe:"cpe:2.3:a:embedthis:appweb"
cpe:"cpe:2.3:a:embedthis:goahead"
cpe:"cpe:2.3:a:exim:exim"
cpe:"cpe:2.3:a:gitlist:gitlist"
cpe:"cpe:2.3:a:google:web_server"
cpe:"cpe:2.3:a:jfrog:artifactory"
cpe:"cpe:2.3:a:kentico:kentico"
cpe:"cpe:2.3:a:koha:koha"
cpe:"cpe:2.3:a:konghq:docker-kong"
cpe:"cpe:2.3:a:laurent_destailleur:awstats"
cpe:"cpe:2.3:a:lighttpd:lighttpd"
cpe:"cpe:2.3:a:microsoft:internet_information_server"
cpe:"cpe:2.3:a:modx:modx_revolution"
cpe:"cpe:2.3:a:nodebb:nodebb"
cpe:"cpe:2.3:a:nodejs:node.js"
cpe:"cpe:2.3:a:openvpn:openvpn_access_server"
cpe:"cpe:2.3:a:openwebanalytics:open_web_analytics"
cpe:"cpe:2.3:a:oracle:glassfish_server"
cpe:"cpe:2.3:a:oracle:iplanet_web_server"
cpe:"cpe:2.3:a:php:php"
cpe:"cpe:2.3:a:prestashop:prestashop"
cpe:"cpe:2.3:a:proftpd:proftpd"
cpe:"cpe:2.3:a:public_knowledge_project:open_journal_systems"
cpe:"cpe:2.3:a:pulsesecure:pulse_connect_secure"
cpe:"cpe:2.3:a:rubyonrails:rails"
cpe:"cpe:2.3:a:sensiolabs:symfony"
cpe:"cpe:2.3:a:typo3:typo3"
cpe:"cpe:2.3:a:vmware:rabbitmq"
cpe:"cpe:2.3:a:webedition:webedition_cms"
cpe:"cpe:2.3:a:zend:zend_server"
cpe:"cpe:2.3:h:zte:f460"
cpe:"cpe:2.3:o:canonical:ubuntu_linux"
cpe:"cpe:2.3:o:fedoraproject:fedora"
cpe:"cpe:2.3:o:microsoft:windows"
"DIR-845L"
eBridge_JSessionid
'ecology_JSessionid'
ecology_JSessionid
elastic indices
"ElasticSearch"
ESMTP
/geoserver/
Graylog
'hash:1357418825'
html:"access_tokens.db"
html:"ACE 4710 Device Manager"
html:"ActiveCollab Installer"
html:"Administration - Installation - MantisBT"
html:"Satis"
html:"Akeeba Backup"
html:"Amazon EC2 Status"
html:"anonymous-cli-metrics.json"
html:"ANTEEO"
html:"anyproxy"
html:"Apache Tomcat"
html:"Apdisk"
html:"appveyor.yml"
html:"aquatronica"
html:"Argo CD"
html:"Ariang"
html:"ASPNETCORE_ENVIRONMENT"
html:"atlassian-connect.json"
html:"atomcms"
html:"auth.json"
html:"authorization token is empty"
html:"Avaya Aura"
html:"AVideo"
html:"AWS EC2 Auto Scaling Lab"
html:"azure-pipelines.yml"
html:"babel.config.js"
html:"behat.yml"
html:"BeyondTrust"
html:"BIG-IP APM"
html:"BIG-IP Configuration Utility"
html:"bitbucket-pipelines.yml"
"html:\"/bitrix/\""
html:"blazor.boot.json"
html:"Blesta installer"
html:"blob.core.windows.net"
html:"buildAssetsDir" "nuxt"
html:"Calibre"
html:"camaleon_cms"
html:"Cargo.lock"
html:"Cargo.toml"
html:"CasaOS"
html:"Cassia Bluetooth Gateway Management Platform"
html:"/certenroll"
html:"/cfadmin/img/"
html:"Change Detection"
html:"Cisco Expressway"
html:"cisco firepower management"
html:"Cisco Unity Connection"
html:"/citrix/xenapp"
html:"ckan 2.8.2" || html:"ckan 2.3"
html:"cloud-config.yml"
html:"CMS Made Simple Install/Upgrade"
html:"codeception.yml"
html:"CodeMeter"
html:"CodiMD"
html:"config.rb"
html:"config.ru"
html:'content="eArcu'
html:"content="Navidrome""
html:"ContentPanel SetupWizard"
html:"contexts known to this"
html:"Coolify" html:"register"
html:"Couchbase Sync Gateway"
html:"Cox Business"
html:"credentials.db"
html:"Crontab UI"
html:"CrushFTP"
html:"cyberpanel"
html:"CyberPanel"
html:"DashRenderer"
html:"Dataease"
html:"data-xwiki-reference"
"html=\"Decision Center Enterprise console\""
html:"Decision Center Enterprise console"
html:"DefectDojo Logo"
html:"def_wirelesspassword"
html:"Dell OpenManage Switch Administrator"
'html:"desktop.ini"'
html:"DSR-250"
html:"DXR.axd"
html:"Easy Installer by ViserLab"
html:"editorconfig"
html:"EJBCA Enterprise Cloud Configuration Wizard"
html:"engage - Portail soignant"
html:"epihash"
html:"eShop Installer"
html:"ETL3100"
html:"FacturaScripts installer"
html:"faradayApp"
html:"Femtocell Access Point"
html:"FileCatalyst file transfer solution"
html:"FleetCart"
html:"FleetCart - Installation"
html:"Forgejo"
html:"FortiPortal"
html:"F-Secure Policy Manager"
html:ftpconfig
html:"ganglia_form.submit()"
html:"Generated by The Webalizer"
html:"GeniusOcean Installer"
html:"gitlab-ci.yml"
html:"GitLab Enterprise Edition"
html:"git web interface version"
html:"go.mod"
html:"gradio_mode"
html:"Guardfile"
html:"HAL Management Console"
html:"hgignore"
html:"Home - CUPS"
html:"HomeWorks Illumination Web Keypad"
html:"Honeywell Building Control"
html:"https://hugegraph.github.io"
html:"human.aspx"
html:"ibmdojo"
html:"iClock Automatic"
html:"IDP Skills Installer"
html:"imgproxy"
html:"Installation" html:"itop"
html:"Installation Panel"
html:"Installer - GROWI"
html:"Install Flarum"
html:"Install - StackPosts"
html:"Install the script - JustFans"
html:"instance_metadata"
html:"Invicti Enterprise - Installation Wizard"
html:"Invoice Ninja Setup"
html:"JBossWS"
html:"JK Status Manager"
html:"jsconfig.json"
html:"jwks.json"
html:"karma.conf.js"
html:"Kemp Login Screen"
html:"LANCOM Systems GmbH"
html:"Laragon" html:"phpinfo"
html:"lesshst"
html:"LibreNMS Install"
html:"Limesurvey Installer"
html:"LMSZAI - Learning Management System"
html:"LoadMaster"
html:"Locklizard Web Viewer"
html:"Login - Jorani"
html:"Login - Netflow Analyzer"
html:"Login | Splunk"
html:"Logon Error Message"
html:"logstash"
"html:\"Lucee\""
html:"Lychee-installer"
html:"Magento Installation"
html:"Magnolia is a registered trademark"
html:mailmap
html:"manifest.json"
html:"MasterSAM"
html:"Mautic Installation"
html:"mempool-space" || title:"Signet Explorer"
html:"Mercurial repositories index"
html:"mongod"
html:"mooSocial Installation"
html:"mysql_history"
html:"/_next/static"
html:"NGINX+ Dashboard"
html:"Nginx Proxy Manager"
html:"nginxWebUI"
html:"ng-version="
html:"nopCommerce Installation"
html:"npm-debug.log"
html:"npm-shrinkwrap.json"
html:"Ocp-Apim-Subscription-Key"
html:"omniapp"
html:"onedev.io"
html:"Open Journal Systems"
html:"Orbit Telephone System"
html:"Orchard Setup - Get Started"
html:"osCommerce"
html:"OWA CONFIG SETTINGS"
html:"owncast"
html:"packages.config"
html:"parameters.yml"
html:"PDI Intellifuel"
html:"phinx.yml"
html:"php_cs.cache"
html:"phpcs.xml"
html:"phpdebugbar"
html:"/phpgedview.db"
html:"phpipam installation wizard"
html:"phpIPAM IP address management"
html:"PHPJabbers"
html:"phpLDAPadmin"
html:"phplist"
html:"phpspec.yml"
html:"phpstan.neon"
html:"phpSysInfo"
html:"pipeline.yaml"
html:"Pipfile"
html:"Piwigo" html:"- Installation"
html:"Plausible"
html:"pnpm-lock.yaml"
html:"polyfill.io"
html:"Portal Setup"
html:"PowerChute Network Shutdown"
html:"Powered by Gitea"
"html:\"PowerShell Universal\""
html:"private gpt"
html:"Procfile"
html:"/productsalert"
html:"ProfitTrailer Setup"
html:"ProjectSend"
html:"ProjectSend setup"
html:"protractor.conf.js"
html:"Provide a link that opens Word"
html:"psalm.xml"
html:"pubspec.yaml"
html:"pyload"
html:"pypiserver"
html:"pyproject.toml"
html:"python_gc_objects_collected_total"
html:"QuickCMS Installation"
html:"QVidium Management"
html:"radarr"
html:"RaidenMAILD"
html:"Rakefile"
html:"readarr"
html:"README.MD"
html:"Redash Initial Setup"
html:"redis.conf"
html:"redis.exceptions.ConnectionError"
html:"request-baskets"
html:"rollup.config.js"
html:"rubocop.yml"
html:"SABnzbd Quick-Start Wizard"
html:"Safeguard for Privileged Passwords"
html:"Saia PCD Web Server"
html:"Salia PLCC"
html:"SAP"
html:"sass-lint.yml"
html:"scrutinizer.yml"
html:"SDT-CW3B1"
html:"searchreplacedb2.php"
html:'Select a frequency for snapshot retention'
html:"sendgrid.env"
html:"Sentinel License Monitor"
html:"server_databases.php"
html:"Serv-U"
html:settings.py
html:"Setup GLPI"
html:"Setup - jfa-go"
html:"sftp.json"
html:"shopping cart program by zen cart"
html:"SimpleHelp"
html:"Sitecore"
html:"Snipe-IT Setup"
html:"sonarr"
html:"Sorry, the requested URL"
html:"stackposts"
html:"Struts Problem Report"
html:"Symmetricom SyncServer"
html:"thisIDRACText"
html:"Tiny File Manager"
html:"Admin Console"
html:"title=\"blue yonder\""
html:'title="Lucy'
html:"PDNU"
html:"prowlarr"
html:"Stash"
html:"Webinterface"
html:"tox.ini"
html:"Traccar"
html:"travis.yml"
"html:\"Trilium Notes\""
html:"TurboMeeting"
html:"/tvcmsblog"
html:"Twig Runtime Error"
html:'Twisted' html:"python"
html:"Ubersmith Setup"
html:"UEditor"
html:"UPS Network Management Card 4"
html:"UrBackup - Keeps your data safe"
html:"/userRpm/"
html:"utnserver Control Center"
html:"UVDesk Helpdesk Community Edition - Installation Wizard"
html:"uwsgi.ini"
html:"Vagrantfile"
html:"Veeam Backup"
html:"Veritas NetBackup OpsCenter Analytics"
html:"Versa Networks"
html:"Viminfo"
html:"VinChin"
html:"Virtual SmartZone"
html:"vite.config.js"
html:"vmw_nsx_logo-black-triangle-500w.png"
html:"voyager-assets"
html:"/vsaas/v2/static/"
html:"/waroot/style.css"
html:"webpack.config.js"
html:"webpackJsonpzipkin-lens"
html:"webpack.mix.js"
"html:\"welcome.cgi?p=logo\""
html:"Welcome to CakePHP"
html:"Welcome to Espocrm"
html:"Welcome to Express"
html:"Welcome to Nginx"
html:"Welcome to Openfire Setup"
html:"Welcome to Progress Application Server for OpenEdge"
html:"Welcome to the Ruckus"
html:"Welcome to Vtiger CRM"
html:"Welcome to your Strapi app"
html:"Welcome to your Strapi app" html:"create an administrator"
html:"Werkzeug powered traceback interpreter"
html:".wget-hsts"
html:".wgetrc"
html:"WhatsUp Gold"
html:"Whisparr"
html:"Whitelabel Error Page"
html:"window.nps"
html:"WN530HG4"
html:"WN531G3"
html:"WN533A8"
html:"wpad.dat"
html:"wp-cli.yml"
html:"/wp-content/plugins/flexmls-idx"
html:"/wp-content/plugins/learnpress"
html:"/wp-content/plugins/really-simple-ssl"
html:"/wp-content/plugins/tutor/"
html:"Writebook"
html:"XBackBone Installer"
html:"/xipblog"
html:XploitSPY
html:"yii\base\ErrorException"
html:"Your Azure Function App is up and running"
html:"Zebra Technologies"
html:"zzcms"
html:"ZzzCMS"
'HTTP/1.0 401 Please Authenticate\r\nWWW-Authenticate: Basic realm="Please Login"'
http.component:"Adobe ColdFusion"
http.component:"Adobe Experience Manager"
http.component:"atlassian confluence"
http.component:"Atlassian Confluence"
http.component:"atlassian jira"
http.component:"Atlassian Jira"
http.component:"Bitbucket"
http.component:"BitBucket"
http.component:"drupal"
http.component:"Drupal"
http.component:"Dynamicweb"
http.component:"ghost"
http.component:"Joomla"
http.component:"magento"
http.component:"Magento"
http.component:"October CMS"
"http.component:\"prestashop\""
http.component:"prestashop"
http.component:"Prestashop"
http.component:"PrestaShop"
http.component:"RoundCube"
http.component:"Subrion"
http.component:"TeamCity"
http.component:"TYPO3"
http.component:"vBulletin"
http.component:zk http.title:"Server Backup Manager"
http.favicon.hash:-1005691603
http.favicon.hash:1011076161
http.favicon.hash:-1013024216
http.favicon.hash:1017650009
http.favicon.hash:1052926265
http.favicon.hash:106844876
http.favicon.hash:-1074357885
http.favicon.hash:1090061843
http.favicon.hash:1099097618
http.favicon.hash:1099370896
http.favicon.hash:-1101206929
http.favicon.hash:"-1105083093"
http.favicon.hash:-1117549627
http.favicon.hash:-1127895693
http.favicon.hash:"-1148190371"
http.favicon.hash:115295460
http.favicon.hash:116323821
http.favicon.hash:11794165
http.favicon.hash:-1197926023
http.favicon.hash:1198579728
http.favicon.hash:1199592666
http.favicon.hash:1212523028
http.favicon.hash:-1215318992
"http.favicon.hash:-121681558"
http.favicon.hash:-121681558
http.favicon.hash:"-1217039701"
http.favicon.hash:-1224668706
http.favicon.hash:-1247684400
http.favicon.hash:1249285083
http.favicon.hash:-1250474341
http.favicon.hash:-1258058404
http.favicon.hash:-1261322577
http.favicon.hash:1262005940
http.favicon.hash:-1264095219
http.favicon.hash:-1292923998,-1166125415
http.favicon.hash:-1295577382
http.favicon.hash:-1298131932
http.favicon.hash:-130447705
http.favicon.hash:1337147129
"http.favicon.hash:-1341442175"
http.favicon.hash:-1343712810
http.favicon.hash:-1350437236
http.favicon.hash:1354079303
http.favicon.hash:1357234275
http.favicon.hash:-1373456171
http.favicon.hash:-1379982221
http.favicon.hash:"1380908726"
http.favicon.hash:1380908726
http.favicon.hash:-1381126564
http.favicon.hash:-1383463717
http.favicon.hash:1386054408
http.favicon.hash:1398055326
http.favicon.hash:1410071322
http.favicon.hash:-1414548363
http.favicon.hash:-1416464161
http.favicon.hash:1460499495
http.favicon.hash:1464851260
http.favicon.hash:-1465760059
http.favicon.hash:-1478287554
http.favicon.hash:-1495233116
http.favicon.hash:-1496590341
http.favicon.hash:1499876150
http.favicon.hash:-1499940355
http.favicon.hash:-1529860313
http.favicon.hash:1540720428
http.favicon.hash:-1548359600
http.favicon.hash:1550906681
http.favicon.hash:1552322396
http.favicon.hash:-1575154882
http.favicon.hash:-1595726841
http.favicon.hash:1604363273
http.favicon.hash:1606029165
http.favicon.hash:-1606065523
http.favicon.hash:-1649949475
http.favicon.hash:1653394551
http.favicon.hash:-1653412201
http.favicon.hash:"-165631681"
http.favicon.hash:-1663319756
http.favicon.hash:-1680052984
http.favicon.hash:1691956220
http.favicon.hash:1693580324
http.favicon.hash:"-1706783005"
http.favicon.hash:-1706783005
http.favicon.hash:1749354953
http.favicon.hash:176427349
http.favicon.hash:-178113786
http.favicon.hash:1781653957
http.favicon.hash:-1797138069
http.favicon.hash:1817615343
http.favicon.hash:1828614783
http.favicon.hash:"-1830859634"
http.favicon.hash:-186961397
http.favicon.hash:-1893514038
http.favicon.hash:1895809524
http.favicon.hash:-1898583197
http.favicon.hash:1903390397
http.favicon.hash:-1950415971
http.favicon.hash:-1951475503
http.favicon.hash:1952289652
http.favicon.hash:-1961736892
http.favicon.hash:-1970367401
http.favicon.hash:-2017596142
http.favicon.hash:-2017604252
http.favicon.hash:2019488876
http.favicon.hash:-2028554187
http.favicon.hash:-2032163853
http.favicon.hash:-2051052918
http.favicon.hash:2056442365
"http.favicon.hash:206985584"
http.favicon.hash:-2073748627 || http.favicon.hash:-1721140132
http.favicon.hash:2099342476
http.favicon.hash:2104916232
http.favicon.hash:"-211006074"
http.favicon.hash:-211006074
http.favicon.hash:-2115208104
http.favicon.hash:2124459909
http.favicon.hash:213144638
http.favicon.hash:2134367771
http.favicon.hash:-2144699833
http.favicon.hash:-219625874
"http.favicon.hash:-234335289"
http.favicon.hash:"24048806"
http.favicon.hash:24048806
http.favicon.hash:-244067125
http.favicon.hash:262502857
http.favicon.hash:-266008933
http.favicon.hash:-283003760
http.favicon.hash:-286484075
http.favicon.hash:305412257
http.favicon.hash:321591353
http.favicon.hash:-347188002
http.favicon.hash:362091310
http.favicon.hash:-374133142
http.favicon.hash:-399298961
http.favicon.hash:407286339
http.favicon.hash:-417785140
http.favicon.hash:-418614327
http.favicon.hash:419828698
http.favicon.hash:431627549
http.favicon.hash:-43504595
http.favicon.hash:439373620
http.favicon.hash:440258421
http.favicon.hash:-440644339
http.favicon.hash:450899026
http.favicon.hash:464587962
http.favicon.hash:487145192
http.favicon.hash:-50306417
http.favicon.hash:-516760689
http.favicon.hash:523757057
http.favicon.hash:538583492
http.favicon.hash:540706145
http.favicon.hash:557327884
http.favicon.hash:-578216669
http.favicon.hash:587330928
http.favicon.hash:-594722214
http.favicon.hash:598296063
http.favicon.hash:-601917817
http.favicon.hash:-608690655
http.favicon.hash:-629968763
http.favicon.hash:-633512412
http.favicon.hash:635899646
http.favicon.hash:"-646322113"
http.favicon.hash:-655683626
http.favicon.hash:657337228
http.favicon.hash:662709064
http.favicon.hash:"-670975485"
"http.favicon.hash:-697231354"
http.favicon.hash:698624197
"http.favicon.hash:\"702863115\""
http.favicon.hash:"702863115"
http.favicon.hash:702863115clear
http.favicon.hash:733091897
http.favicon.hash:739801466
http.favicon.hash:-741491222
http.favicon.hash:-749942143
http.favicon.hash:751911084
"http.favicon.hash:762074255"
http.favicon.hash:762074255
http.favicon.hash:781922099
http.favicon.hash:786533217
http.favicon.hash:-800060828
http.favicon.hash:-800551065
http.favicon.hash:"801517258"
http.favicon.hash:-81573405
http.favicon.hash:816588900
http.favicon.hash:824580113
http.favicon.hash:-82958153
http.favicon.hash:-831756631
http.favicon.hash:"-839356603"
http.favicon.hash:-850502287
http.favicon.hash:855432563
"http.favicon.hash:868509217"
http.favicon.hash:"871154672"
http.favicon.hash:873381299
http.favicon.hash:874152924
http.favicon.hash:876876147
http.favicon.hash:889652940
http.favicon.hash:-902890504
http.favicon.hash:-916902413
http.favicon.hash:-919788577
http.favicon.hash:932345713
http.favicon.hash:933976300
http.favicon.hash:942678640
http.favicon.hash:957255151
http.favicon.hash:965982073
http.favicon.hash:967636089
http.favicon.hash:969374472
http.favicon.hash:-976853304
http.favicon.hash:-977323269
http.favicon.hash:981081715
http.favicon.hash:983734701
http.favicon.hash:988422585
http.favicon.hash:989289239
http.favicon.hash:999357577
http.html:"4DACTION/"
http.html:"74cms"
http.html:"academy lms"
http.html:"Ampache Update"
http.html:"Apache Airflow"
http.html:"Apache Axis"
http.html:"Apache Cocoon"
http.html:"Apache OFBiz"
http.html:"Apache Solr"
http.html:"Apache Solr"
http.html:"apollo-adminservice"
http.html:"app.2fe6356cdd1ddd0eb8d6317d1a48d379.css"
http.html:"artica"
http.html:".asmx?WSDL"
http.html:"Audiocodes"
http.html:"BeyondInsight"
"http.html:\"BeyondTrust Privileged Remote Access Login\""
http.html:"bigant"
http.html:"BigAnt Admin"
http.html:"/bitrix/"
http.html:"blogengine.net"
http.html:"BMC Remedy"
http.html:"Camunda Welcome"
http.html:"car rental management system"
http.html:"Car Rental Management System"
http.html:"/CasaOS-UI/public/index.html"
http.html:"CCM - Authentication Failure"
http.html:"Check Point Mobile"
http.html:"chronoslogin.js"
http.html:"CMS Quilium"
http.html:"Command API Explorer"
http.html:'content="Redmine'
http.html:'content="Smartstore'
http.html:"corebos"
http.html:"crushftp"
http.html:"CS141"
http.html:"Cvent Inc"
http.html:"CxSASTManagerUri"
http.html:"dataease"
http.html:"DedeCms"
http.html:"Delta Controls ORCAview"
http.html:"Develocity Build Cache Node"
http.html:"DLP system"
http.html:"/dokuwiki/"
http.html:"dotnetcms"
http.html:"Dufs"
http.html:"dzzoffice"
http.html:"E-Mobile"
http.html:"E-Mobile "
http.html:EmpireCMS
http.html:"ESP Easy Mega"
http.html:"eZ Publish"
http.html:"Flatpress"
http.html:"Fuji Xerox Co., Ltd"
http.html:"Get_Verify_Info"
http.html:"glpi"
http.html:"Gnuboard"
http.html:"gnuboard5"
http.html:"GoAnywhere Managed File Transfer"
http.html:"Gradle Enterprise Build Cache Node"
http.html:"H3C-SecPath-运维审计系统"
http.html_hash:1015055567
http.html_hash:1076109428
http.html_hash:-14029177
http.html_hash:-1957161625
http.html_hash:510586239
http.html:"HG532e"
http.html:"hospital management system"
http.html:"Hospital Management System"
http.html:'Hugo'
http.html:"Huly"
http.html:"i3geo"
http.html:"IBM WebSphere Portal"
"http.html:\"import-xml-feed\""
http.html:"import-xml-feed"
http.html:"index.createOpenPad"
http.html:"Interactsh Server"
http.html:"IPdiva"
http.html:"iSpy"
http.html:"JamF"
http.html:"Jamf Pro Setup"
http.html:"Jellyfin"
http.html:"JHipster"
http.html:"JupyterHub"
http.html:"kavita"
http.html:"LANDESK(R)"
http.html:"Laravel FileManager"
http.html:"LISTSERV"
http.html:livezilla
http.html:"Login (Virtual Traffic Manager"
http.html:"lookerVersion"
http.html:"magnusbilling"
http.html:"mailhog"
http.html:"/main/login.lua?pageid="
http.html:"metersphere"
http.html:"MiCollab End User Portal"
http.html:"Micro Focus Application Lifecycle Management"
http.html:"Micro Focus iPrint Appliance"
http.html:"Mirantis Kubernetes Engine"
http.html:"Mitel Networks"
http.html:"MobileIron"
http.html:"moodle"
http.html:"multipart/form-data" html:"file"
http.html:"myLittleAdmin"
http.html:"myLittleBackup"
http.html:"NeoboxUI"
http.html:"Network Utility"
http.html:"Nexus Repository Manager"
http.html:'ng-app="syncthing"'
http.html:"Nordex Control"
http.html:"Omnia MPX"
http.html:"OpenCTI"
http.html:"OpenEMR"
http.html:"opennebula"
http.html:"Oracle HTTP Server"
http.html:"Oracle UIX"
"http.html:\"outsystems\""
http.html:"owncloud"
http.html:"PbootCMS"
http.html:"phpMiniAdmin"
http.html:"phpMyAdmin"
http.html:"phpmyfaq"
http.html:/plugins/royal-elementor-addons/
http.html:"power by dedecms" || title:"dedecms"
http.html:"Powerd by AppCMS"
http.html:"powered by CATALOGcreator"
http.html:"powerjob"
http.html:"processwire"
http.html:provided by projectsend
http.html:"pyload"
http.html:"/redfish/v1"
http.html:"redhat" "Satellite"
http.html:"r-seenet"
http.html:rt_title
http.html:"SAP Analytics Cloud"
http.html:"seafile"
http.html:"Semaphore"
http.html:"sharecenter"
http.html:"SLIMS"
http.html:"SolarView Compact"
http.html:"soplanning"
http.html:"SOUND4"
http.html:"study any topic, anytime"
http.html:"sucuri firewall"
http.html:"symfony Profiler"
http.html:"Symfony Profiler"
http.html:"sympa"
http.html:"teampass"
http.html:"Telerik Report Server"
http.html:"Thruk"
http.html:"thruk" || http.title:"thruk monitoring webinterface"
http.html:"TIBCO BusinessConnect"
http.html:"tiki wiki"
http.html:"TLR-2005KSH"
http.html:"totemomail" inurl:responsiveui
http.html:"Umbraco"
http.html:"vaultwarden"
http.html:"Vertex Tax Installer"
http.html:"VMG1312-B10D"
http.html:"VMware Horizon"
http.html:"VSG1432-B101"
http.html:"wavlink"
http.html:"Wavlink"
http.html:"WebADM"
http.html:"Webasyst Installer"
http.html:"WebCenter"
http.html:"Web Image Monitor"
http.html:"Webp"
http.html:"webshell4"
http.html:"Welcome to MapProxy"
http.html:"Welcome to Oracle Fusion Middleware"
http.html:"wiki.js"
http.html:"window.frappe_version"
http.html:/wp-content/plugins/adsense-plugin/
http.html:"/wp-content/plugins/agile-store-locator/"
http.html:wp-content/plugins/ap-pricing-tables-lite
http.html:/wp-content/plugins/autoptimize
http.html:/wp-content/plugins/backup-backup/
http.html:/wp-content/plugins/bws-google-analytics/
http.html:/wp-content/plugins/bws-google-maps/
http.html:/wp-content/plugins/bws-linkedin/
http.html:/wp-content/plugins/bws-pinterest/
http.html:/wp-content/plugins/bws-smtp/
http.html:/wp-content/plugins/bws-testimonials/
http.html:/wp-content/plugins/chaty/
http.html:/wp-content/plugins/cmp-coming-soon-maintenance/
http.html:/wp-content/plugins/companion-sitemap-generator/
http.html:/wp-content/plugins/contact-form-multi/
http.html:/wp-content/plugins/contact-form-plugin/
http.html:/wp-content/plugins/contact-form-to-db/
http.html:/wp-content/plugins/contest-gallery/
http.html:/wp-content/plugins/controlled-admin-access/
http.html:"wp-content/plugins/crypto"
http.html:/wp-content/plugins/cryptocurrency-widgets-pack/
http.html:/wp-content/plugins/custom-admin-page/
http.html:/wp-content/plugins/custom-facebook-feed/
http.html:/wp-content/plugins/custom-search-plugin/
http.html:/wp-content/plugins/defender-security/
http.html:/wp-content/plugins/ditty-news-ticker/
"http.html:\"/wp-content/plugins/download-monitor/\""
http.html:/wp-content/plugins/error-log-viewer/
http.html:"wp-content/plugins/error-log-viewer-wp"
http.html:/wp-content/plugins/essential-blocks/
"http.html:/wp-content/plugins/extensive-vc-addon/"
http.html:/wp-content/plugins/foogallery/
http.html:/wp-content/plugins/forminator
http.html:/wp-content/plugins/g-auto-hyperlink/
http.html:"/wp-content/plugins/gift-voucher/"
http.html:/wp-content/plugins/gtranslate
http.html:"/wp-content/plugins/hostel/"
http.html:/wp-content/plugins/htaccess/
http.html:"wp-content/plugins/hurrakify"
http.html:/wp-content/plugins/learnpress
http.html:/wp-content/plugins/login-as-customer-or-user
http.html:wp-content/plugins/media-library-assistant
http.html:/wp-content/plugins/motopress-hotel-booking
http.html:/wp-content/plugins/mstore-api/
http.html:/wp-content/plugins/newsletter/
http.html:/wp-content/plugins/nex-forms-express-wp-form-builder/
http.html:"/wp-content/plugins/ninja-forms/"
http.html:/wp-content/plugins/ninja-forms/
http.html:/wp-content/plugins/pagination/
http.html:/wp-content/plugins/paid-memberships-pro/
http.html:/wp-content/plugins/pdf-generator-for-wp
http.html:/wp-content/plugins/pdf-print/
http.html:/wp-content/plugins/photoblocks-grid-gallery/
http.html:/wp-content/plugins/photo-gallery
http.html:/wp-content/plugins/polls-widget/
http.html:/wp-content/plugins/popup-builder/
http.html:/wp-content/plugins/popup-by-supsystic
http.html:/wp-content/plugins/popup-maker/
http.html:/wp-content/plugins/post-smtp
http.html:/wp-content/plugins/prismatic
http.html:/wp-content/plugins/promobar/
http.html:/wp-content/plugins/qt-kentharadio
http.html:/wp-content/plugins/quick-event-manager
http.html:"/wp-content/plugins/radio-player"
http.html:/wp-content/plugins/rating-bws/
http.html:/wp-content/plugins/realty/
http.html:/wp-content/plugins/registrations-for-the-events-calendar/
http.html:/wp-content/plugins/searchwp-live-ajax-search/
http.html:/wp-content/plugins/sender/
http.html:/wp-content/plugins/sfwd-lms
http.html:/wp-content/plugins/shortpixel-adaptive-images/
http.html:/wp-content/plugins/show-all-comments-in-one-page
http.html:/wp-content/plugins/site-offline/
http.html:/wp-content/plugins/social-buttons-pack/
http.html:/wp-content/plugins/social-login-bws/
http.html:/wp-content/plugins/stock-ticker/
http.html:/wp-content/plugins/subscriber/
http.html:/wp-content/plugins/super-socializer/
http.html:/wp-content/plugins/tutor/
http.html:/wp-content/plugins/twitter-plugin/
http.html:/wp-content/plugins/ubigeo-peru/
http.html:/wp-content/plugins/ultimate-member
http.html:/wp-content/plugins/updater/
"http.html:/wp-content/plugins/user-meta/"
http.html:/wp-content/plugins/user-role/
http.html:/wp-content/plugins/video-list-manager/
http.html:/wp-content/plugins/visitors-online/
http.html:/wp-content/plugins/wc-multivendor-marketplace
http.html:/wp-content/plugins/woocommerce-payments
http.html:/wp-content/plugins/wordpress-toolbar/
"http.html:/wp-content/plugins/wp-fastest-cache/"
http.html:"/wp-content/plugins/wp-file-upload/"
http.html:/wp-content/plugins/wp-helper-lite
http.html:/wp-content/plugins/wp-simple-firewall
http.html:/wp-content/plugins/wp-statistics/
http.html:/wp-content/plugins/wp-user/
http.html:/wp-content/plugins/zendesk-help-center/
http.html:/wp-content/themes/newspaper
http.html:/wp-content/themes/noo-jobmonster
http.html:"wp-stats-manager"
http.html:"Wuzhicms"
http.html:"/xibosignage/xibo-cms"
http.html:"yeswiki"
http.html:"Z-BlogPHP"
http.html:"zm - login"
http.html:"ZTE Corporation"
http.html:"心上无垢,林间有风"
http.securitytxt:contact http.status:200
http.title:"1Password SCIM Bridge Login"
http.title:"3CX Phone System Management Console"
http.title:"Accueil WAMPSERVER"
http.title:"Acrolinx Dashboard"
http.title:"Actifio Resource Center"
http.title:"Adapt authoring tool"
http.title:"Admin | Employee's Payroll Management System"
http.title:adminer
http.title:"AdmiralCloud"
http.title:"Adobe Media Server"
http.title:"Advanced eMail Solution DEEPMail"
http.title:"Advanced Setup - Security - Admin User Name & Password"
http.title:"Aerohive NetConfig UI"
http.title:"Aethra Telecommunications Operating System"
http.title:"AirCube Dashboard"
http.title:"AirNotifier"
http.title:"Alamos GmbH | FE2"
http.title:"Alertmanager"
http.title:"Alfresco Content App"
http.title:"AlienVault USM"
http.title:"altenergy power control software"
http.title:"AlternC Desktop"
http.title:"Amazon Cognito Developer Authentication Sample"
http.title:"Amazon ECS Sample App"
http.title:"Ampache -- Debug Page"
http.title:"Android Debug Database"
http.title:"Apache2 Debian Default Page:"
http.title:"Apache2 Ubuntu Default Page"
http.title:"apache apisix dashboard"
http.title:"Apache CloudStack"
http.title:"Apache+Default","Apache+HTTP+Server+Test","Apache2+It+works"
http.title:"Apache HTTP Server Test Page powered by CentOS"
http.title:"apache streampipes"
http.title:"apex it help desk"
http.title:"appsmith"
http.title:"Aptus Login"
http.title:"Aqua Enterprise" || http.title:"Aqua Cloud Native Security Platform"
http.title:"ArcGIS"
http.title:"Argo CD"
http.title:"avantfax - login"
http.title:"aviatrix cloud controller"
http.title:"AVideo"
http.title:"Axel"
http.title:"Axigen WebAdmin"
http.title:"Axigen WebMail"
http.title:"Axway API Manager Login"
http.title:"Axyom Network Manager"
http.title:"Azkaban Web Client"
http.title:"Bagisto Installer"
http.title:"Bamboo"
http.title:"BigBlueButton"
http.title:"BigFix"
http.title:"big-ip®-+redirect" +"server"
http.title:"BioTime"
http.title:"Black Duck"
http.title:"Blue Iris Login"
http.title:"BMC Remedy Single Sign-On domain data entry"
http.title:"BMC Software"
http.title:"browserless debugger"
http.title:"Caton Network Manager System"
http.title:"Celebrus"
http.title:"Centreon"
http.title:"change detection"
http.title:"Charger Management Console"
http.title:"Check_MK"
http.title:"Cisco Secure CN"
http.title:"Cisco ServiceGrid"
http.title:"Cisco Systems Login"
http.title:"Cisco Telepresence"
http.title:"citrix gateway"
http.title:"ClarityVista"
http.title:"CleanWeb"
http.title:"Cloudphysician RADAR"
http.title:"Cluster Overview - Trino"
http.title:"C-more -- the best HMI presented by AutomationDirect"
http.title:"cobbler web interface"
http.title:"Codeigniter Application Installer"
http.title:"code-server login"
http.title:"Codian MCU - Home page"
http.title:"CompleteView Web Client"
http.title:"Conductor UI", http.title:"Workflow UI"
http.title:"Connection - SphinxOnline"
http.title:"Content Central Login"
http.title:"copyparty"
http.title:"Coverity"
http.title:"craftercms"
http.title:"Create a pipeline - Go" html:"GoCD Version"
http.title:"Creatio"
http.title:"Database Error"
http.title:"datagerry"
http.title:"DataHub"
http.title:"datataker"
http.title:"Davantis"
http.title:"Decision Center | Business Console"
http.title:"Dericam"
http.title:"Dgraph Ratel Dashboard"
http.title:"docassemble"
http.title:"Docuware"
http.title:"Dolibarr"
http.title:"dolphinscheduler"
http.title:"DolphinScheduler"
http.title:"Domibus"
http.title:"dotcms"
http.title:"Dozzle"
http.title:"Easyvista"
http.title:"Ekoenergetyka-Polska Sp. z o.o - CCU3 Software Update for Embedded Systems"
http.title:"Elastic" || http.favicon.hash:1328449667
http.title:"Elasticsearch-sql client"
http.title:"emby"
http.title:"emerge"
http.title:"Emerson Network Power IntelliSlot Web Card"
http.title:"EMQX Dashboard"
http.title:"Endpoint Protector"
http.title:"EnvisionGateway"
http.title:"erxes"
http.title:"EWM Manager"
http.title:"Extreme NetConfig UI"
http.title:"Falcosidekick"
http.title:"FastCGI"
http.title:"Flex VNF Web-UI"
http.title:"flightpath"
http.title:"flowchart maker"
http.title:"Forcepoint Appliance"
http.title:"fortimail"
http.title:"FORTINET LOGIN"
http.title:"fortiweb - "
http.title:"fuel cms"
http.title:"GeoWebServer"
http.title:"gitbook"
http.title:"Gitea"
http.title:"GitHub Debug"
http.title:"GitLab"
http.title:"git repository browser"
http.title:"GlassFish Server - Server Running"
http.title:"Glowroot"
http.title:"glpi"
http.title:"Gophish - Login"
http.title:"Grandstream Device Configuration"
http.title:"Graphite Browser"
http.title:"Graylog Web Interface"
http.title:"Gryphon"
http.title:"GXD5 Pacs Connexion utilisateur"
http.title:"H5S CONSOLE"
http.title:"Hacked By"
http.title:"Haivision Gateway"
http.title:"Haivision Media Platform"
http.title:"hd-network real-time monitoring system v2.0"
http.title:"Heatmiser Wifi Thermostat"
http.title:"HiveQueue"
http.title:"Home Assistant"
http.title:"Home Page - My ASP.NET Application"
http.title:"HP BladeSystem"
http.title:"HP Color LaserJet"
http.title:"Hp Officejet pro"
http.title:"HP Virtual Connect Manager"
http.title:"httpbin.org"
http.title:"HTTP Server Test Page powered by CentOS-WebPanel.com"
http.title:"HUAWEI Home Gateway HG658d"
http.title:"Hubble UI"
http.title:"hybris"
http.title:"HYPERPLANNING"
http.title:"IBM-HTTP-Server"
http.title:"IBM iNotes Login"
http.title:"IBM Security Access Manager"
http.title:"Icecast Streaming Media Server"
http.title:"IdentityServer v3"
http.title:"IIS7"
http.title:"IIS Windows Server"
http.title:"ImpressPages installation wizard"
http.title:"Infoblox"
http.title:"Installation - Gogs"
http.title:"Installer - Easyscripts"
http.title:"Intelbras"
http.title:"Intelligent WAPPLES"
http.title:"IoT vDME Simulator"
"http.title:\"ispconfig\""
http.title:"iXBus"
http.title:"J2EE"
http.title:"Jaeger UI"
http.title:"jeedom"
http.title:"Jellyfin"
"http.title:\"JFrog\""
http.title:"Jitsi Meet"
http.title:'JumpServer'
http.title:"Juniper Web Device Manager"
http.title:"JupyterHub"
http.title:"Kafka Center"
http.title:"Kafka Cruise Control UI"
http.title:"kavita"
http.title:"Kerio Connect Client"
http.title:"kibana"
http.title:"kkFileView"
http.title:"Kopano WebApp"
http.title:"Kraken dashboard"
http.title:"Kube Metrics Server"
http.title:"Kubernetes Operational View"
http.title:"kubernetes web view"
http.title:"lansweeper - login"
http.title:"LDAP Account Manager"
http.title:"Leostream"
http.title:"Linksys Smart WI-FI"
http.title:"LinShare"
http.title:"LISTSERV Maestro"
http.title:"LockSelf"
http.title:"login | control webpanel"
http.title:"Log in - easyJOB"
http.title:"Login - Residential Gateway"
http.title:"login - splunk"
http.title:"Login - Splunk"
http.title:"login" "x-oracle-dms-ecid" 200
http.title:"Logitech Harmony Pro Installer"
http.title:"Lomnido Login"
http.title:"Loxone Intercom Video"
http.title:"Lucee"
http.title:"Maestro - LuCI"
http.title:"MAG Dashboard Login"
http.title:"MailWatch Login Page"
http.title:"manageengine desktop central 10"
http.title:"ManageEngine Password"
http.title:"manageengine servicedesk plus"
http.title:"mcloud-installer-web"
http.title:"Meduza Stealer"
http.title:"MetaView Explorer"
http.title:MeTube
http.title:"Microsoft Azure App Service - Welcome"
http.title:"Microsoft Internet Information Services 8"
http.title:"mikrotik routeros > administration"
"http.title:\"mlflow\""
http.title:"mlflow"
http.title:"MobiProxy"
http.title:"MongoDB Ops Manager"
http.title:"mongo express"
http.title:"MSPControl - Sign In"
http.title:"My Datacenter - Login"
http.title:"Mystic Stealer"
http.title:"nagios"
http.title:"nagios xi"
http.title:"N-central Login"
http.title:"nconf"
http.title:"Netris Dashboard"
http.title:"NETSurveillance WEB"
http.title:"NetSUS Server Login"
http.title:"Nextcloud"
http.title:"nginx admin manager"
http.title:"Nginx Proxy Manager"
http.title:"ngrok"
http.title:"Normhost Backup server manager"
http.title:"noVNC"
http.title:"NS-ASG"
http.title:"ntopng - Traffic Dashboard"
http.title:"officescan"
http.title:"okta"
http.title:"Olivetti CRF"
http.title:"olympic banking system"
http.title:"OneinStack"
http.title:"Opcache Control Panel"
http.title:"Open Game Panel"
http.title:"openHAB"
http.title:"OpenObserve"
http.title:"opensis"
http.title:"openSIS"
http.title:"openvpn connect"
http.title:"Operations Automation Default Page"
http.title:"Opinio"
http.title:"opmanager plus"
http.title:"opnsense"
http.title:"opsview"
http.title:"Oracle Application Server Containers"
http.title:"oracle business intelligence sign in"
http.title:"Oracle Containers for J2EE"
http.title:"Oracle Database as a Service"
"http.title:\"Oracle PeopleSoft Sign-in\""
http.title:"Oracle(R) Integrated Lights Out Manager"
http.title:"OrangeHRM Web Installation Wizard"
http.title:"OSNEXUS QuantaStor Manager"
http.title:"otobo"
http.title:"OurMGMT3"
http.title:outlook exchange
http.title:"OVPN Config Download"
http.title:"PAHTool"
http.title:"pandora fms"
http.title:"Passbolt | Open source password manager for teams"
http.title:"Payara Server - Server Running"
http.title:"PendingInstallVZW - Web Page Configuration"
http.title:"Pexip Connect for Web"
http.title:"pfsense - login"
http.title:"PgHero"
http.title:"PGP Global Directory"
http.title:"phoronix-test-suite"
http.title:PhotoPrism
http.title:"PHP Mailer"
http.title:phpMyAdmin
http.title:"PHP warning" || "Fatal error"
http.title:"Plastic SCM"
http.title:"Please Login | Nozomi Networks Console"
http.title:"PMM Installation Wizard"
http.title:"posthog"
http.title:"PowerCom Network Manager"
http.title:"Powered By Jetty"
http.title:"Powered by lighttpd"
http.title:"PowerJob"
http.title:"prime infrastructure"
http.title:"PRONOTE"
http.title:"Puppetboard"
http.title:"Ranger - Sign In"
http.title:"rconfig"
http.title:"rConfig"
http.title:"RD Web Access"
http.title:"Remkon Device Manager"
http.title:"Reolink"
http.title:"rocket.chat"
http.title:"Rocket.Chat"
http.title:"RouterOS router configuration page"
http.title:"roxy file manager"
http.title:"R-SeeNet"
http.title:"seagate nas - seagate"
http.title:SearXNG
http.title:"Secure Login Service"
http.title:"securenvoy"
http.title:"securepoint utm"
http.title:"SeedDMS"
http.title:"Selenium Grid"
http.title:"Self Enrollment"
http.title:"SequoiaDB"
http.title:"Server Backup Manager SE"
http.title:"Service"
http.title:"SevOne NMS - Network Manager"
http.title:"S-Filer"
http.title:"SGP"
http.title:"SHOUTcast Server"
http.title:"sidekiq"
http.title:"Sign In - Hyperic"
http.title:"Sign in to Netsparker Enterprise"
"http.title:\"SimpleSAMLphp installation page\""
http.title:"sitecore"
http.title:"Skeepers"
http.title:"SMS Gateway | Installation"
http.title:"smtp2go"
http.title:"Snapdrop"
http.title:"SoftEther VPN Server"
http.title:"SOGo"
http.title:"Sonatype Nexus Repository"
http.title:"Splunk"
http.title:"Splunk SOAR"
http.title:"SQL Buddy"
http.title:"SteVe - Steckdosenverwaltung"
http.title:"storybook"
http.title:"strapi"
http.title:"Supermicro BMC Login"
"http.title:\"swagger\""
http.title:"Symantec Encryption Server"
http.title:"Synapse Mobility Login"
http.title:"t24 sign in"
http.title:"Tactical RMM - Login"
http.title:"Tenda 11N Wireless Router Login Screen"
http.title:"Test Page for the Apache HTTP Server on Red Hat Enterprise Linux"
http.title:"Test Page for the HTTP Server on Fedora"
http.title:"Test Page for the Nginx HTTP Server on Amazon Linux"
http.title:"Test Page for the SSL/TLS-aware Apache Installation on Web Site"
http.title:"The install worked successfully! Congratulations!"
http.title:"thinfinity virtualui"
http.title:"TileServer GL - Server for vector and raster maps with GL styles"
"http.title:\"tixeo\""
http.title:"totolink"
http.title:"traefik"
http.title:"transact sign in","t24 sign in"
http.title:"Transmission Web Interface"
http.title:triconsole.com - php calendar date picker
http.title:"TurnKey OpenVPN"
http.title:"Twenty"
http.title:"TYPO3 Exception"
http.title:"UI for Apache Kafka"
http.title:"UiPath Orchestrator"
http.title:"UniFi Network"
http.title:"UniGUI"
http.title:"Verizon Router"
http.title:"VERSA DIRECTOR Login"
http.title:"vertigis"
http.title:"ViewPoint System Status"
http.title:"vRealize Operations Tenant App"
http.title:"Wallix Access Manager"
http.title:"Warning [refreshed every 30 sec.]"
http.title:"Watershed LRS"
http.title:"webcamXP 5"
http.title:"webmin"
http.title:"Web Server's Default Page"
http.title:"WebSphere Liberty"
http.title:"Webtools"
http.title:"Web Transfer Client"
http.title:"web viewer for samsung dvr"
http.title:"Welcome to Citrix Hypervisor"
http.title:"Welcome to CodeIgniter"
http.title:"Welcome to nginx!"
http.title:"welcome to ntop"
http.title:"Welcome to OpenResty!"
http.title:"Welcome To RunCloud"
http.title:"Welcome to Service Assistant"
http.title:"Welcome to Sitecore"
http.title:"Welcome to Symfony"
http.title:"Welcome to tengine"
http.title:"Welcome to VMware Site Recovery Manager"
http.title:"Welcome to your Strapi app"
http.title:"Wi-Fi APP Login"
http.title:"Wiren Board Web UI"
http.title:"WoodWing Studio Server"
http.title:"XAMPP"
http.title:"XDS-AMR - status"
http.title:"XenForo"
http.title:"XNAT"
http.title:"YApi"
http.title:zblog
http.title:"zentao"
http.title:"zeroshell"
http.title:"Zope QuickStart"
http.title:"zywall"
http.title:"ZyWall"
http.title:"小米路由器"
http.title:"高清智能录播系统"
icon_hash="915499123"
"If you find a bug in this Lighttpd package, or in Lighttpd itself"
imap
"Kerio Control"
Laravel-Framework
ldap
"Lorex"
"loytec"
"Max-Forwards:"
Microsoft FTP Service
mongodb server information
"Ms-Author-Via: DAV"
MSMQ
"nimplant C2 server"
"OfficeWeb365"
ollama
"Ollama is running"
OpenSSL
"Open X Server:"
Path=/gespage
pentaho
"pfBlockerNG"
php.ini
"PHPnow works"
".phpunit.result.cache"
pop3 port:110
port:10001
"port:110"
port:"111"
port:11300 "cmd-peek"
port:1433
port:22
port:2375 product:"docker"
port:23 telnet
"port:3306"
port:3310 product:"ClamAV"
port:3310 product:"ClamAV" version:"0.99.2"
"port:445"
port:445
port:523
'port:541 xab'
port:5432
port:5432 product:"PostgreSQL"
"port:69"
port:"79" action
port:"873"
port:873
product:"ActiveMQ OpenWire transport"
product:"Apache ActiveMQ"
product:'Ares RAT C2'
product:"Axigen"
product:"besu"
product:"BGP"
product:"bitvise"
"product:\"Check Point Firewall\""
product:"Cisco fingerd"
product:"cloudflare-nginx"
product:"CouchDB"
"product:cups"
product:"CUPS (IPP)"
product:'DarkComet Trojan'
product:'DarkTrack RAT Trojan'
product:"Dropbear sshd"
product:"Erigon"
product:"Erlang Port Mapper Daemon"
product:"etcd"
"product:\"Exim smtpd\""
product:"Fortinet FortiWiFi"
product:"Geth"
product:"GitLab Self-Managed"
product:"GNU Inetutils FTPd"
product:"HttpFileServer httpd"
product:"IBM DB2 Database Server"
product:"jenkins"
product:"Kafka"
product:"kubernetes"
product:"Kubernetes" version:"1.21.5-eks-bc4871b"
product:"Linksys E2000 WAP http config"
product:"MikroTik router ftpd"
product:"MikroTik RouterOS API Service"
product:"Minecraft"
product:"MS .NET Remoting httpd"
product:"mysql"
product:"MySQL"
product:"Nethermind"
product:"Niagara Fox"
product:"nPerf"
product:OpenEthereum
product:"OpenResty"
product:"OpenSSH"
product:"Oracle TNS Listener"
product:"Oracle Weblogic"
product:'Orcus RAT Trojan'
"product:\"PostgreSQL\""
"product:\"ProFTPD\""
product:"ProFTPD"
product:"RabbitMQ"
product:"rhinosoft serv-u httpd"
product:"Riak"
product:"Sliver C2"
product:"TeamSpeak 3 ServerQuery"
product:"tomcat"
product:"VMware Authentication Daemon"
product:"vsftpd"
product:"Xlight ftpd"
product:'XtremeRAT Trojan'
'"python/3.10 aiohttp/3.8.3" && bad status'
"r470t"
realm="karaf"
"RTM WEB"
"RT-N16"
RTSP/1.0
secmail
"SEH HTTP Server"
"Server: Boa/"
"Server: Burp Collaborator"
'Server: Cleo'
'Server: Cleo'
"Server: EC2ws"
'server: "ecstatic"'
'Server: Flowmon'
"Server: gabia"
"Server: GeoHttpServer"
'Server: Goliath'
'Server: httpd/2.0 port:8080'
'Server: mikrotik httpproxy'
'Server: Mongoose'
"Server: tinyproxy"
"Server: Trellix"
"Set-Cookie: MFPSESSIONID="
'set-cookie: nsbase_session'
sickbeard
smtp
SSH-2.0-AWS_SFTP_1.1
"SSH-2.0-MOVEit"
SSH-2.0-ROSSSH
ssl:"AsyncRAT Server"
ssl.cert.issuer.cn:"QNAP NAS",title:"QNAP Turbo NAS"
ssl.cert.serial:146473198
ssl.cert.subject.cn:"Onimai Academies CA"
ssl.cert.subject.cn:"Quasar Server CA"
ssl:"Covenant" http.component:"Blazor"
ssl.jarm:07d14d16d21d21d07c42d41d00041d24a458a375eef0c576d23a7bab9a9fb1+port:443
ssl:"Kubernetes Ingress Controller Fake Certificate"
ssl:"MetasploitSelfSignedCA"
ssl:"Mythic"
ssl:Mythic port:7443
ssl:"ou=fortianalyzer"
ssl:"ou=fortiauthenticator"
ssl:"ou=fortiddos"
ssl:"ou=fortigate"
ssl:"ou=fortimanager"
ssl:"P18055077"
'ssl:postalCode=3540 ssl.jarm:3fd21b20d00000021c43d21b21b43de0a012c76cf078b8d06f4620c2286f5e'
ssl.version:sslv2 ssl.version:sslv3 ssl.version:tlsv1 ssl.version:tlsv1.1
"Statamic"
".styleci.yml"
The requested resource
"TIBCO Spotfire Server"
title:"3ware"
title:"Acunetix"
title:"AddOnFinancePortal"
title:"Administration login" html:"poste<span"
title:"AdminLogin - MPFTVC"
title:"Advanced System Management"
title:"AeroCMS"
title:"AiCloud"
title:"Airflow - DAGs"
title:"Akuiteo"
title:"Alma Installation"
title:"Ambassador Edge Stack"
title:"AmpGuard wifi setup"
title:"Anaqua User Sign On""
title:"AnythingLLM"
title:"Apache APISIX Dashboard"
title:"Apache Apollo"
title:"Apache Drill"
title:"Apache Druid"
title:"Apache Miracle Linux Web Server"
title:"Apache Ozone"
title:"Apache Pinot"
title:"Apache Shiro Quickstart"
title:"apache streampipes"
title:"Apache Tomcat"
title:"APC | Log On"
title:"Appliance Management Console Login"
title:"Appliance Setup Wizard"
title:"Audiobookshelf"
title:"Automatisch"
title:"AutoSet"
title:"AWS X-Ray Sample Application"
title:"Axigen"
title:"Backpack Admin"
title:"Bamboo setup wizard"
title:"BigAnt"
title:"Biostar"
title:"Blackbox Exporter"
title:"BRAVIA Signage"
title:"BrightSign"
title:"Build Dashboard - Atlassian Bamboo"
title:"Businesso Installer"
title:"c3325"
title:"cAdvisor"
title:"Camaleon CMS"
title:"CAREL Pl@ntVisor"
"title:\"CData - API Server\""
"title:\"CData Arc\""
"title:\"CData Connect\""
"title:\"CData Sync\""
title:"Chamilo has not been installed"
title:"Change Detection"
title:"Choose your deployment type - Confluence"
title:"Cisco Unified"
title:"Cisco vManage"
title:"Cisco WebEx"
title:"Claris FileMaker WebDirect"
title:"CloudCenter Installer"
title:"CloudCenter Suite"
title:"Cloud Services Appliance"
title:"Codis • Dashboard"
title:"Collectd Exporter"
title:"Coming Soon"
title:"COMPALEX"
title:"Concourse"
title:"Configure ntop"
title:"Congratulations | Cloud Run"
title="ConnectWise Control Remote Support Software"
title:"copyparty"
title:"Cryptobox"
title:"CudaTel"
title:"cvsweb"
title:"CyberChef"
title:"Dashboard - Ace Admin"
title:"Dashboard - Bootstrap Admin Template"
title:"Dashboard - Confluence"
title:"Dashboard - ESPHome"
title:"Datadog"
title:"dataiku"
title:"Debug Config"
title:"Debugger"
"title=\"Decision Center | Business Console\""
title:"dedecms" || http.html:"power by dedecms"
title:"Default Parallels Plesk Panel Page"
title:"Dell Remote Management Controller"
title:"Deluge"
title:"Devika AI"
title:"Dialogic XMS Admin Console"
title:"Discourse Setup"
title:"Discuz!"
title:"D-LINK"
title:"Dockge"
title:"Docmosis Tornado"
title:"DokuWiki"
title:"Dolibarr install or upgrade"
title:"DPLUS Dashboard"
title:"DQS Superadmin"
title:"Dradis Professional Edition"
title:"DuomiCMS"
title:"Dynamics Container Host"
title:"EC2 Instance Information"
title:"Eclipse BIRT Home"
title:"Elastic HD Dashboard"
title:"Elemiz Network Manager"
title:"elfinder"
title:"Enablix"
title:"Encompass CM1 Home Page"
title:"Enterprise-Class Redis for Developers"
title:"Envoy Admin"
title:"EOS HTTP Browser"
title:"Error" html:"CodeIgniter"
title:"Eureka"
title:"Event Debug Server"
title:"EVlink Local Controller"
title:"Express Status"
title:"FASTPANEL HOSTING CONTROL"
title:"ffserver Status"
title:"FileGator"
title:"Flahscookie Superadmin"
title:"Flask + Redis Queue + Docker"
title:"Flexnet"
title:"Flex VNF Web-UI"
title:"FlureeDB Admin Console"
title:"FootPrints Service Core Login"
title:"For the Love of Music - Installation"
title:"FOSSBilling"
title:"Freshrss"
title:"Froxlor"
title:"Froxlor Server Management Panel"
title:"FusionAuth Setup Wizard"
title:"Gargoyle Router Management Utility"
title:"GEE Server"
title:"Geowebserver"
title:"Gira HomeServer 4"
title:"Gitblit"
title:"GitHub Enterprise"
title:"GitLab"
title:"GitList"
title:"GL.iNet Admin Panel"
title:"Global Traffic Statistics"
title:"Glowroot"
title:"Gopher Server"
title:"Gradio"
title:"Grafana"
title:"GraphQL Playground"
title:"Gravitino"
title:"Grav Register Admin User"
title:"Graylog Web Interface"
title:"Group-IB Managed XDR"
title:"H2O Flow"
title:"haproxy exporter"
title:"Health Checks UI"
title:"Hetzner Cloud"
title:"HFS /"
title:"Homebridge"
title:"Home - Mongo Express"
title:"Home Page - Select or create a notebook"
title:"Honeywell XL Web Controller"
title:"hookbot"
title:"hoteldruid"
title:"h-sphere"
title:"HUAWEI"
title:"Hue Personal"
title:"hue personal wireless lighting"
title:"Hue - Welcome to Hue"
title:"HugeGraph"
title:"Hybris"
title:"HyperTest"
title:"Icecast Streaming Media Server"
title:"icewarp"
title:"IDEMIA"
title:"i-MSCP - Multi Server Control Panel"
title:"Initial server configuration"
'title:"Installation - Gitea: Git with a cup of tea"'
title:"Installation Moodle"
title:"Install Binom"
title:"Install concrete"
title:"Installing TYPO3 CMS"
title:"Install · Nagios Log Server"
title:"Install Umbraco"
title:"ISPConfig" http.favicon.hash:483383992
title:"issabel"
title:"ITRS"
title:"Jackett"
title:"Jamf Pro"
title:"JC-e converter webinterface"
title:"Jeecg-Boot"
title:"Jeedom"
title:"JIRA - JIRA setup"
title:"Jitsi Meet"
title:"Joomla Web Installer"
title:"JSON Server"
title:"JSPWiki"
title:"Juniper Web Device Manager"
title:"jupyter notebook"
title:"Kafka-Manager"
title:"keycloak"
title:"Kiali"
title:"Kiwi TCMS - Login" http.favicon.hash:-1909533337
title:"KnowledgeTree Installer"
title:"Koel"
title:kubecost
title:Kube-state-metrics
title:"Lantronix"
title:"LDAP Account Manager"
title:"LibrePhotos"
title:"LibreSpeed"
title:"Libvirt"
title:"Lidarr"
title:"Liferay"
title:"Lightdash"
title:"LinkTap Gateway"
title:"Locust"
title:logger html:"htmlWebpackPlugin.options.title"
title:"Login - Authelia"
title:"Log in - Bitbucket"
title:"Login | Control WebPanel"
title:"Login | GYRA Master Admin"
title:"login" product:"Avtech"
title:"login" product:"Avtech AVN801 network camera"
title:"Log in | Telerik Report Server"
title:"Login to ICC PRO system"
title:"Login to TLR-2005KSH"
title:"LVM Exporter"
title:"MachForm Admin Panel"
title:"macOS Server"
title:"Magnolia Installation"
title:"Maltrail"
title:"MAMP"
title:"ManageEngine"
title:"ManageEngine Desktop Central"
title:"MantisBT"
title:"Matomo"
title:"Mautic"
title:"Metabase"
title:"Microsoft Azure Web App - Error 404"
title:"MinIO Console"
title:"mirth connect administrator"
title:"Mobotix"
title:"MobSF"
title:"Moleculer Microservices Project"
title:"MongoDB exporter"
'title:"Monstra :: Install"'
title:"Moodle"
title:"MySQLd exporter"
title:"myStrom"
title:"Nacos"
title:"Nagios XI"
title:"Named Process Exporter"
title:"NeoDash"
title:"Netdisco"
title:"Netman"
title:"netman 204"
title:"NetMizer"
"title:NextChat,\"ChatGPT Next Web\""
title:"NginX Auto Installer"
title="nginxwebui"
title:"Nifi"
"title:\"NiFi\""
title:"NiFi"
title:"NI Web-based Configuration & Monitoring"
title:"NodeBB Web Installer"
title:"NoEscape - Login"
title:"Notion – One workspace. Every team."
title:"NP Data Cache"
title:"NPort Web Console"
title:"nsqadmin"
title:"Nuxeo Platform"
title:"O2 Easy Setup"
title=="O2OA"
title:"OCS Inventory"
title:"Odoo"
title:"Okta"
title:"OLT Web Management Interface"
title:"OneDev"
title:"OpenCart"
title:"opencats"
title:"OpenEMR Setup Tool"
title:"OpenMage Installation Wizard"
title:"OpenMediaVault"
title:"OpenNMS Web Console"
title:"openproject"
title:"OpenShift"
title:"OpenShift Assisted Installer"
title:"openSIS"
title:"OpenWRT"
title:"Oracle Application Server"
title:"Oracle Forms"
title:"Oracle Opera" && html:"/OperaLogin/Welcome.do"
title:"Oracle PeopleSoft Sign-in"
title:"Orangescrum Setup Wizard"
title:"osticket"
title:"osTicket"
title:"Ovirt-Engine"
title:"owncloud"
title:"OXID eShop installation"
title:"Pa11y Dashboard"
title:"Pagekit Installer"
title:"PairDrop"
title:"Papercut"
'title:"Payara Micro #badassfish - Error report"'
title:"PCDN Cache Node Dataset"
title:"pCOWeb"
title:"Pega"
title:"perfSONAR"
title:" Permissions | Installer"
title:"Persis"
title:"PgHero"
title:"Pgwatch2"
title:"phpLDAPadmin"
title:"phpMemcachedAdmin"
title:"phpmyadmin"
title:"Pi-hole"
title:"Piwik › Installation"
title:"Plenti"
title:"Portainer"
title:"Postgres exporter"
title:"Powered by phpwind"
title:"Powered By vBulletin"
title:"PQube 3"
title:"PrestaShop Installation Assistant"
title:"Prison Management System"
title:"Pritunl"
title:"PrivateBin"
title:"PrivX"
title:"ProcessWire 3.x Installer"
title:"Pulsar Admin"
'title:"PuppetDB: Dashboard"'
title:"QlikView - AccessPoint"
title:"QuestDB · Console"
title:"RabbitMQ Exporter"
title:"Raspberry Shake Config"
title:"Ray Dashboard"
title:"rConfig"
title:"ReCrystallize"
title:"RedisInsight"
title:"Redpanda Console"
title:"Registration and Login System"
title:"Rekognition Image Validation Debug UI"
title:"reNgine"
title:"Reolink"
title:"Repetier-Server"
title:"ResourceSpace"
title:"Retool"
title:"RocketMQ"
title:"Room Alert"
title:"RStudio Sign In"
title:"ruckus"
"title:\"Rule Execution Server\""
title:"Rule Execution Server"
title:"Rundeck"
title:"Runtime Error"
title:"Rustici Content Controller"
title:"SaltStack Config"
title:"Sato"
title:"Scribble Diffusion"
title:"ScriptCase"
title:"SecurEnvoy"
title:SecuritySpy
title:"SelfCheck System Manager"
title:"SentinelOne - Management Console"
title:"Seq"
title:"SERVER MONITOR - Install"
title:"ServerStatus"
title:"servicenow"
title:"- setup" html:"Modem setup"
title:"Setup - mosparo"
title:"Setup wizard for webtrees"
title:"Setup Wizard" html:"/ruckus"
title:"Setup Wizard" html:"untangle"
title:"Setup Wizard" http.favicon.hash:-1851491385
title:"Setup Wizard" http.favicon.hash:2055322029
title:"ShareFile Storage Server"
title:"shenyu"
title:"Shopify App — Installation"
title:"shopware AG"
title:"ShopXO企业级B2C电商系统提供商"
title:"Sign In - Airflow"
title:"sitecore"
title:"Sitecore"
title:"Slurm HPC Dashboard"
title:"SmartPing Dashboard"
title:"SMF Installer"
title:"SmokePing Latency Page for Network Latency Grapher"
title:"Snoop Servlet"
title:"SoftEther VPN Server"
title:"Solr"
title:"Sonarqube"
title:"SonicWall Network Security"
title:"Speedtest Tracker"
title:"Splash"
title:"SqWebMail"
title:"Stremio-Jackett"
title:"Struts2 Showcase"
title:"Sugar Setup Wizard"
title:"SuiteCRM"
title:"SumoWebTools Installer"
title:"Superadmin UI - 4myhealth"
title:"SuperWebMailer"
title:"Symantec Endpoint Protection Manager"
title:"Synapse is running"
title:"SyncThru Web Service"
title:"System Properties"
title:"T24 Sign in"
title:"tailon"
title:"TamronOS IPTV系统"
title:"Tasmota"
title:"Tautulli - Welcome"
title:"TeamForge :"
title:"Tekton"
title:"TemboSocial Administration"
title:"Tenda Web Master"
title:"Teradek Cube Administrative Console"
title:"TestRail Installation Wizard"
title:"Thanos | Highly available Prometheus setup"
title:"ThinkPHP"
title:"THIS WEBSITE HAS BEEN SEIZED"
title:"Tigase XMPP Server"
title:"Tiki Wiki CMS"
title:"Tiny File Manager"
title:"Tiny Tiny RSS - Installer"
title:"TitanNit Web Control"
title:"tooljet"
title:"ToolJet - Dashboard"
title:"topaccess"
title:"Tornado - Login"
title:"Trassir Webview"
title:"Turbo Website Reviewer"
title:"TurnKey LAMP"
title:"ueditor"
title:"UniFi Wizard"
title:"uniGUI"
title:"Uptime Kuma"
title:"User Control Panel"
title:"USG FLEX"
title:"Utility Services Administration"
title:"UVDesk Helpdesk Community Edition - Installation Wizard"
title:"V2924"
title:"V2X Control"
"title:\"vBulletin\""
title:"veeam backup enterprise manager"
title:"Veeam Backup for GCP"
title:"Veeam Backup for Microsoft Azure"
title:"Veriz0wn"
title:"VideoXpert"
title:"Vitogate 300"
title:"VIVOTEK Web Console"
title:"vManage"
title:"VMware Appliance Management"
title:"VMware Aria Operations"
title:"VMware Carbon Black EDR"
title:"Vmware Cloud"
title:"VMware Cloud Director Availability"
title:"VMWARE FTP SERVER"
title:"VMware HCX"
title:"Vmware Horizon"
title:"VMware Site Recovery Manager"
title:"VMware VCenter"
title:"Vodafone Vox UI"
title:"vRealize Operations Manager"
title:"WAMPSERVER Homepage"
"title:\"Wazuh\""
title:"WebCalendar Setup Wizard"
title:"WebcomCo"
title:"Web Configurator"
title:"Web Configurator" html:"ACTi"
title:"Web File Manager"
title:"WebIQ"
title:"Webmin"
title:"Webmodule"
title:"WebPageTest"
title:"Webroot - Login"
title:"Webuzo Installer"
title:"Welcome to Azure Container Instances!"
title:"Welcome to C-Lodop"
title:"Welcome to Movable Type"
title:"Welcome to SmarterStats!"
title:"Welcome to your SWAG instance"
title:"WhatsUp Gold" http.favicon.hash:-2107233094
title:"WIFISKY-7层流控路由器"
title:"Wiki.js Setup"
title:"WorldServer"
title:"WoW-CMS | Installation"
title:"XenMobile"
"title:\"XenMobile - Console\""
title:"XEROX WORKCENTRE"
title:"xfinity"
title:"xnat"
title:"X-UI Login"
title:"Yellowfin Information Collaboration"
title:"Yii Debugger"
title:"Yopass"
title:"Your Own URL Shortener"
title:"YzmCMS"
title:"Zebra"
title:"Zend Server Test Page"
title:"Zenphoto install"
title:"Zeppelin"
title:"Zitadel"
title:"ZoneMinder"
title:"ZWave To MQTT"
title:"контроллер"
title:"孚盟云 "
title:"通达OA"
"Versa-Analytics-Server"
"wasabis3"
"/wd/hub"
"/websm/"
"Wing FTP Server"
"WL-500G"
"WL-520GU"
"workerman"
"WSO2 Carbon Server"
"www-authenticate:"
'www-authenticate: negotiate'
X-Amz-Server-Side-Encryption
"X-AspNetMvc-Version"
"X-AspNet-Version"
"X-ClickHouse-Summary"
"X-Influxdb-"
"X-Jenkins"
"X-Mod-Pagespeed:"
"X-Powered-By: Chamilo"
"X-Powered-By: Express"
"X-Powered-By: PHP"
"X-Recruiting:"
"X-TYPO3-Parsetime: 0ms"
Find devices in a particular city. city:"Bangalore"
Find devices in a particular country. country:"IN"
Find devices by giving geographical coordinates. geo:"56.913055,118.250862"
country:us country:ru country:de city:chicago
Find devices matching the hostname. server: "gws" hostname:"google" hostname:example.com -hostname:subdomain.example.com hostname:example.com,example.org
Find devices based on an IP address or /x CIDR. net:210.214.0.0/16
org:microsoft org:"United States Department"
asn:ASxxxx
Find devices based on operating system. os:"windows 7"
Find devices based on open ports. proftpd port:21
Find devices before or after between a given time. apache after:22/02/2009 before:14/3/2010
Self signed certificates ssl.cert.issuer.cn:example.com ssl.cert.subject.cn:example.com
Expired certificates ssl.cert.expired:true
ssl.cert.subject.cn:example.com
device:firewall device:router device:wap device:webcam device:media device:"broadband router" device:pbx device:printer device:switch device:storage device:specialized device:phone device:"voip" device:"voip phone" device:"voip adaptor" device:"load balancer" device:"print server" device:terminal device:remote device:telecom device:power device:proxy device:pda device:bridge
os:"windows 7" os:"windows server 2012" os:"linux 3.x"
product:apache product:nginx product:android product:chromecast
cpe:apple cpe:microsoft cpe:nginx cpe:cisco
server: nginx server: apache server: microsoft server: cisco-ios
dc:14:de:8e:d7:c1:15:43:23:82:25:81:d2:59:e8:c0
http.html:/dana-na
http.title:"Index of /" http.html:".pem"
onion-location
"product:MySQL" mysql port:"3306"
"product:MongoDB" mongodb port:27017
"MongoDB Server Information { "metrics":" "Set-Cookie: mongo-express=" "200 OK" "MongoDB Server Information" port:27017 -authentication
kibana content-legth:217
port:9200 json port:"9200" all:elastic port:"9200" all:"elastic indices"
"product:Memcached"
"product:CouchDB" port:"5984"+Server: "CouchDB/2.1.0"
"port:5432 PostgreSQL"
"port:8087 Riak"
"product:Redis"
"product:Cassandra"
"Server: Prismview Player"
"in-tank inventory" port:10001
No auth required to access CLI terminal. "privileged command" GET
P372 "ANPR enabled"
mikrotik streetlight
"voter system serial" country:US
May allow for ATM Access availability NCR Port:"161"
"Cisco IOS" "ADVIPSERVICESK9_LI-M"
"[2J[H Encartele Confidential"
http.title:"Tesla PowerPack System" http.component:"d3" -ga3ca4f2
"Server: gSOAP/2.8" "Content-Length: 583"
Shodan made a pretty sweet Ship Tracker that maps ship locations in real time, too!
"Cobham SATCOM" OR ("Sailor" "VSAT")
title:"Slocum Fleet Mission Control"
"Server: CarelDataServer" "200 Document follows"
http.title:"Nordex Control" "Windows 2000 5.0 x86" "Jetty/3.1 (JSP 1.1; Servlet 2.2; java 1.6.0_14)"
"[1m[35mWelcome on console"
Secured by default, thankfully, but these 1,700+ machines still have no business being on the internet.
"DICOM Server Response" port:104
"Server: EIG Embedded Web Server" "200 Document follows"
"Siemens, SIMATIC" port:161
"Server: Microsoft-WinCE" "Content-Length: 12581"
"HID VertX" port:4070
"log off" "select the appropriate"
Helps to find the charging status of tesla powerpack. http.title:"Tesla PowerPack System" http.component:"d3" -ga3ca4f2
title:"xzeres wind"
"html:"PIPS Technology ALPR Processors""
"port:502"
"port:1911,4911 product:Niagara"
"port:18245,18246 product:"general electric""
"port:5006,5007 product:mitsubishi"
"port:2455 operating system"
"port:102"
"port:47808"
"port:5094 hart-ip"
"port:9600 response code"
"port:2404 asdu address"
"port:20000 source address"
"port:44818"
"port:1962 PLC"
"port:789 product:"Red Lion Controls"
"port:20547 PLC"
"authentication disabled" port:5900,5901 "authentication disabled" "RFB 003.008"
99.99% are secured by a secondary Windows login screen.
"\x03\x00\x00\x0b\x06\xd0\x00\x00\x124\x00"
product:"cobalt strike team server" product:"Cobalt Strike Beacon" ssl.cert.serial:146473198 - default certificate serial number ssl.jarm:07d14d16d21d21d07c42d41d00041d24a458a375eef0c576d23a7bab9a9fb1 ssl:foren.zik
http.html_hash:-1957161625 product:"Brute Ratel C4"
ssl:"Covenant" http.component:"Blazor"
ssl:"MetasploitSelfSignedCA"
Routers which got compromised hacked-router-help-sos
product:"Redis key-value store"
Find Citrix Gateway. title:"citrix gateway"
Command-line access inside Kubernetes pods and Docker containers, and real-time visualization/monitoring of the entire infrastructure.
title:"Weave Scope" http.favicon.hash:567176827
"X-Jenkins" "Set-Cookie: JSESSIONID" http.title:"Dashboard"
Jenkins Unrestricted Dashboard x-jenkins 200
"Docker Containers:" port:2375
"Docker-Distribution-Api-Version: registry" "200 OK" -gitlab
"dnsmasq-pi-hole" "Recursion: enabled"
"port: 53" Recursion: Enabled
"root@" port:23 -login -password -name -Session
NO password required for telnet access. port:23 console gateway
"polycom command shell"
nport -keyin port:23
A tangential result of Google's sloppy fractured update approach. 🙄 More information here.
"Android Debug Bridge" "Device" port:5555
Lantronix password port:30718 -secured
"Citrix Applications:" port:1604
Vulnerable (kind of "by design," but especially when exposed).
"smart install client active"
PBX "gateway console" -password port:23
http.title:"- Polycom" "Server: lighttpd" "Polycom Command Shell" -failed port:23
"Polycom Command Shell" -failed port:23
Example: Polycom Video Conferencing
"Server: Bomgar" "200 OK"
"Intel(R) Active Management Technology" port:623,664,16992,16993,16994,16995 "Active Management Technology"
HP-ILO-4 !"HP-ILO-4/2.53" !"HP-ILO-4/2.54" !"HP-ILO-4/2.55" !"HP-ILO-4/2.60" !"HP-ILO-4/2.61" !"HP-ILO-4/2.62" !"HP-iLO-4/2.70" port:1900
"Press Enter for Setup Mode port:9999"
Helps to find the cleartext wifi passwords in Shodan. html:"def_wirelesspassword"
The wp-config.php if accessed can give out the database credentials. http.html:"* The wp-config.php creation script uses this file"
"x-owa-version" "IE=EmulateIE7" "Server: Microsoft-IIS/7.0"
"x-owa-version" "IE=EmulateIE7" http.favicon.hash:442749392
"X-AspNet-Version" http.title:"Outlook" -"x-owa-version"
"X-MS-Server-Fqdn"
Produces ~500,000 results...narrow down by adding "Documents" or "Videos", etc.
"Authentication: disabled" port:445
"Authentication: disabled" NETLOGON SYSVOL -unix port:445
"Authentication: disabled" "Shared this folder to access QuickBooks files OverNetwork" -unix port:445
"220" "230 Login successful." port:21
"Set-Cookie: iomega=" -"manage/login.html" -http.title:"Log In"
Redirecting sencha port:9000
"Server: Logitech Media Server" "200 OK"
Example: Logitech Media Servers
"X-Plex-Protocol" "200 OK" port:32400
"CherryPy/5.1.0" "/home"
"IPC$ all storage devices"
title:camera
webcam has_screenshot:true
"d-Link Internet Camera, 200 OK"
"Hipcam RealServer/V1.0"
"Server: yawcam" "Mime-Type: text/html"
("webcam 7" OR "webcamXP") http.component:"mootools" -401
"Server: IP Webcam Server" "200 OK"
html:"DVR_H264 ActiveX"
With username:admin and password: :P NETSurveillance uc-httpd Server: uc-httpd 1.0.0
"Serial Number:" "Built:" "Server: HP HTTP"
ssl:"Xerox Generic Root"
"SERVER: EPSON_Linux UPnP" "200 OK"
"Server: EPSON-HTTP" "200 OK"
"Server: KS_HTTP" "200 OK"
"Server: CANON HTTP Server"
"Server: AV_Receiver" "HTTP/1.1 406"
Apple TVs, HomePods, etc.
"\x08_airplay" port:5353
"Chromecast:" port:8008
"Model: PYNG-HUB"
"Server: calibre" http.status:200 http.title:calibre
title:"OctoPrint" -title:"Login" http.favicon.hash:1307375944
"ETH - Total speed"
Substitute .pem with any extension or a filename like phpinfo.php.
http.title:"Index of /" http.html:".pem"
Exposed wp-config.php files containing database credentials.
http.html:"* The wp-config.php creation script uses this file"
"Minecraft Server" "protocol 340" port:25565
net:175.45.176.0/22,210.52.109.0/24,77.94.35.0/24
The payment card giant MasterCard just fixed a glaring error in its domain name server settings that could have allowed anyone to intercept or divert Internet traffic for the company by registering an unused domain name. The misconfiguration persisted for nearly five years until a security researcher spent $300 to register the domain and prevent it from being grabbed by cybercriminals.
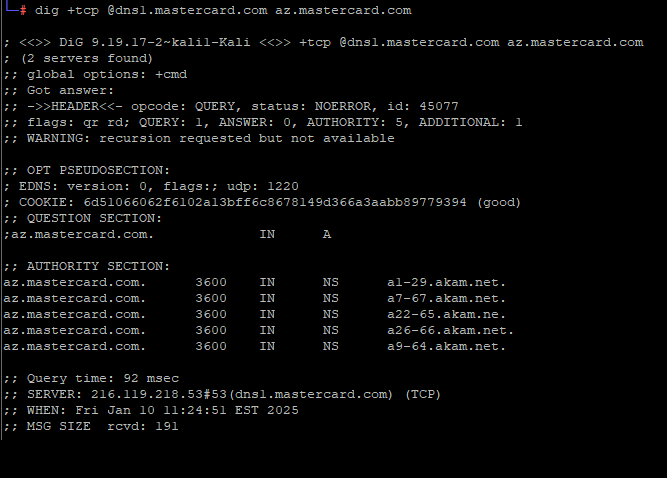
A DNS lookup on the domain az.mastercard.com on Jan. 14, 2025 shows the mistyped domain name a22-65.akam.ne.
From June 30, 2020 until January 14, 2025, one of the core Internet servers that MasterCard uses to direct traffic for portions of the mastercard.com network was misnamed. MasterCard.com relies on five shared Domain Name System (DNS) servers at the Internet infrastructure provider Akamai [DNS acts as a kind of Internet phone book, by translating website names to numeric Internet addresses that are easier for computers to manage].
All of the Akamai DNS server names that MasterCard uses are supposed to end in “akam.net” but one of them was misconfigured to rely on the domain “akam.ne.”
This tiny but potentially critical typo was discovered recently by Philippe Caturegli, founder of the security consultancy Seralys. Caturegli said he guessed that nobody had yet registered the domain akam.ne, which is under the purview of the top-level domain authority for the West Africa nation of Niger.
Caturegli said it took $300 and nearly three months of waiting to secure the domain with the registry in Niger. After enabling a DNS server on akam.ne, he noticed hundreds of thousands of DNS requests hitting his server each day from locations around the globe. Apparently, MasterCard wasn’t the only organization that had fat-fingered a DNS entry to include “akam.ne,” but they were by far the largest.
Had he enabled an email server on his new domain akam.ne, Caturegli likely would have received wayward emails directed toward mastercard.com or other affected domains. If he’d abused his access, he probably could have obtained website encryption certificates (SSL/TLS certs) that were authorized to accept and relay web traffic for affected websites. He may even have been able to passively receive Microsoft Windows authentication credentials from employee computers at affected companies.
But the researcher said he didn’t attempt to do any of that. Instead, he alerted MasterCard that the domain was theirs if they wanted it, copying this author on his notifications. A few hours later, MasterCard acknowledged the mistake, but said there was never any real threat to the security of its operations.
“We have looked into the matter and there was not a risk to our systems,” a MasterCard spokesperson wrote. “This typo has now been corrected.”
Meanwhile, Caturegli received a request submitted through Bugcrowd, a program that offers financial rewards and recognition to security researchers who find flaws and work privately with the affected vendor to fix them. The message suggested his public disclosure of the MasterCard DNS error via a post on LinkedIn (after he’d secured the akam.ne domain) was not aligned with ethical security practices, and passed on a request from MasterCard to have the post removed.
MasterCard’s request to Caturegli, a.k.a. “Titon” on infosec.exchange.
Caturegli said while he does have an account on Bugcrowd, he has never submitted anything through the Bugcrowd program, and that he reported this issue directly to MasterCard.
“I did not disclose this issue through Bugcrowd,” Caturegli wrote in reply. “Before making any public disclosure, I ensured that the affected domain was registered to prevent exploitation, mitigating any risk to MasterCard or its customers. This action, which we took at our own expense, demonstrates our commitment to ethical security practices and responsible disclosure.”
Most organizations have at least two authoritative domain name servers, but some handle so many DNS requests that they need to spread the load over additional DNS server domains. In MasterCard’s case, that number is five, so it stands to reason that if an attacker managed to seize control over just one of those domains they would only be able to see about one-fifth of the overall DNS requests coming in.
But Caturegli said the reality is that many Internet users are relying at least to some degree on public traffic forwarders or DNS resolvers like Cloudflare and Google.
“So all we need is for one of these resolvers to query our name server and cache the result,” Caturegli said. By setting their DNS server records with a long TTL or “Time To Live” — a setting that can adjust the lifespan of data packets on a network — an attacker’s poisoned instructions for the target domain can be propagated by large cloud providers.
“With a long TTL, we may reroute a LOT more than just 1/5 of the traffic,” he said.
The researcher said he’d hoped that the credit card giant might thank him, or at least offer to cover the cost of buying the domain.
“We obviously disagree with this assessment,” Caturegli wrote in a follow-up post on LinkedIn regarding MasterCard’s public statement. “But we’ll let you judge— here are some of the DNS lookups we recorded before reporting the issue.”
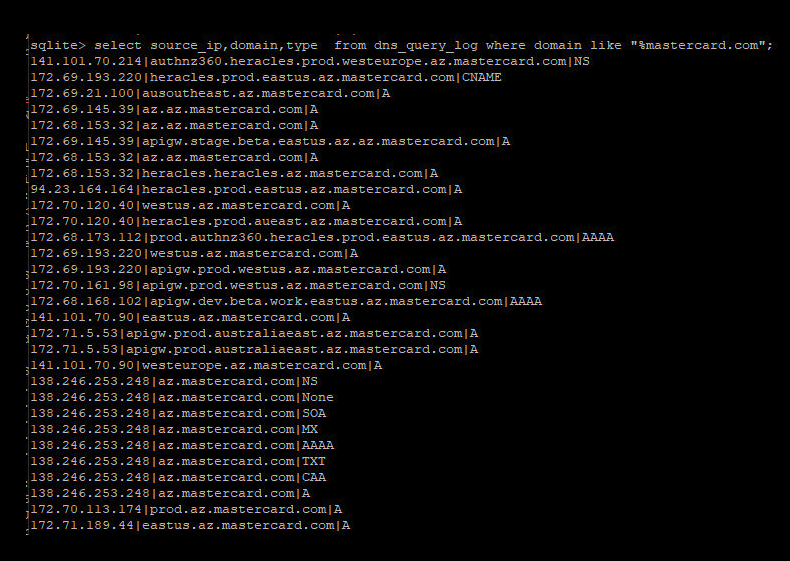
Caturegli posted this screenshot of MasterCard domains that were potentially at risk from the misconfigured domain.
As the screenshot above shows, the misconfigured DNS server Caturegli found involved the MasterCard subdomain az.mastercard.com. It is not clear exactly how this subdomain is used by MasterCard, however their naming conventions suggest the domains correspond to production servers at Microsoft’s Azure cloud service. Caturegli said the domains all resolve to Internet addresses at Microsoft.
“Don’t be like Mastercard,” Caturegli concluded in his LinkedIn post. “Don’t dismiss risk, and don’t let your marketing team handle security disclosures.”
One final note: The domain akam.ne has been registered previously — in December 2016 by someone using the email address um-i-delo@yandex.ru. The Russian search giant Yandex reports this user account belongs to an “Ivan I.” from Moscow. Passive DNS records from DomainTools.com show that between 2016 and 2018 the domain was connected to an Internet server in Germany, and that the domain was left to expire in 2018.
This is interesting given a comment on Caturegli’s LinkedIn post from an ex-Cloudflare employee who linked to a report he co-authored on a similar typo domain apparently registered in 2017 for organizations that may have mistyped their AWS DNS server as “awsdns-06.ne” instead of “awsdns-06.net.” DomainTools reports that this typo domain also was registered to a Yandex user (playlotto@yandex.ru), and was hosted at the same German ISP — Team Internet (AS61969).